Microsoft Teams permissions
Table of contents
Microsoft Teams is one of the fastest-growing products in Microsoft’s history. Two years ago, when Teams became available, there was an across-the-board suspicion about its future. Not without reason: Microsoft’s attempts in social collaboration were not always successful. They would frequently try a lot of different things to see what worked. SharePoint got its social features in 2013, which were soon made redundant by acquiring Yammer. Slack even wrote an “open letter” to Microsoft (https://slackhq.com/dear-microsoft), teasingly explaining to them how to collaborate.
Soon it became clear that Microsoft would place all its bets on Teams. Luckily, I had the privilege of being in the preview program right from the start. Microsoft was listening to its partners, customers, and us MVPs from day one. With collective voice, structured chat with bots and integrations, and a completely new concept of tabs, where users could configure their custom applications within the teams, it was a winning idea from the start.
There are some things even today, which don’t work as they should (khm, khm.. switching identities based on multiple identities and tenants based on those identities), but in general, the direction was good. Now they have a better integration of Teams with SharePoint, Power Apps, and Planner. Information workers now have a powerful “cockpit” where they can do a good portion of their work. Soon – way sooner than anyone would have expected – Slack was regretting that open letter.
Why we need Microsoft Teams governance
However, with products and services that get adopted that easily, customers will eventually need to think about governance. How many Teams do we have in the company? Who created them in the past, and who can create them now? The files are stored in SharePoint Online, but how do Teams permissions work with SharePoint permissions? What happens when a user shares a file from SharePoint, and how is it different from sharing using Teams? How do you handle external users?
This blog post will tackle those and other questions related to Microsoft Teams governance. We will discuss who is allowed to create Teams within your environment.
Who can create a new team in Microsoft Teams?
The answer to the first question – who can create Teams in your environment is easy, and not always a satisfactory one: everyone can. I know companies who stopped their Teams rollout in only a few weeks after they got a few thousand Teams in their environment. This is the moment when we can clearly see that we need a governance plan from day one when rolling out Microsoft Teams. “Adding” governance later is possible, but more difficult.
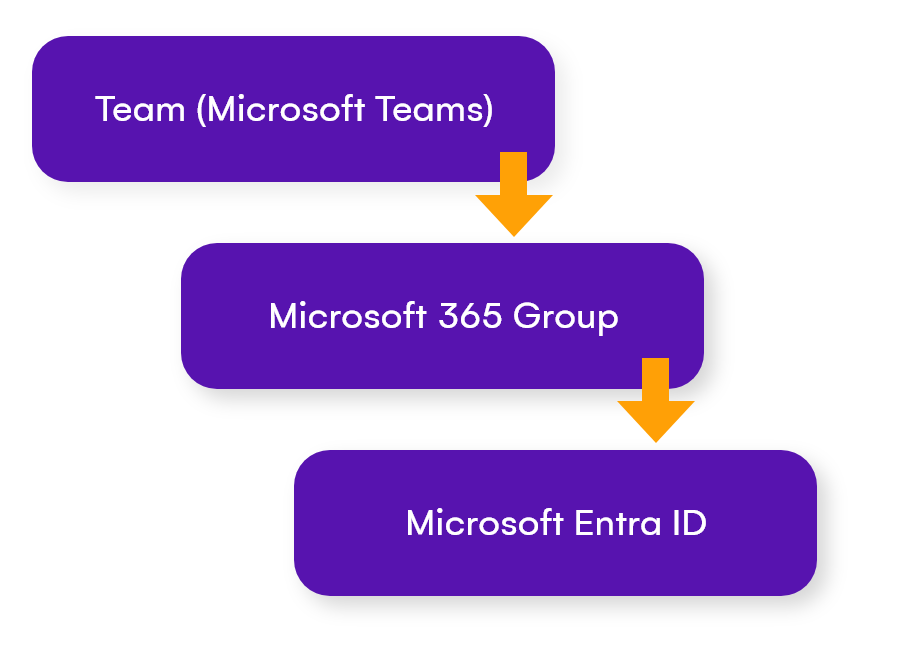
Microsoft Teams and Microsoft 365 groups (previously Office 365 Groups) are complimentary, and whoever can create a group in Microsoft 365 Groups, can also create Teams. Giving everyone permission to create Microsoft 365 groups is a generally bad idea in the first place (which also means creating all the other Group-based Office 365 services, such as Microsoft Planner), so the best way would be limiting the number of users who can create Microsoft 365 groups.
Making changes in Microsoft Entra ID
However, Microsoft 365 Groups are just representations of the Microsoft Entra ID (previously Azure AD) groups inside the Azure Portal, and this is where we need to make some changes.
When we navigate to the Microsoft Entra admin center, we can find our Groups under the Identity category, and under Groups, select “All Groups” . This is where you will see ALL the groups from your tenant. The groups that are created through Microsoft 365 and have related interfaces (such as when creating new Teams, Plans, etc.) will be marked with the “Microsoft 365” group type.
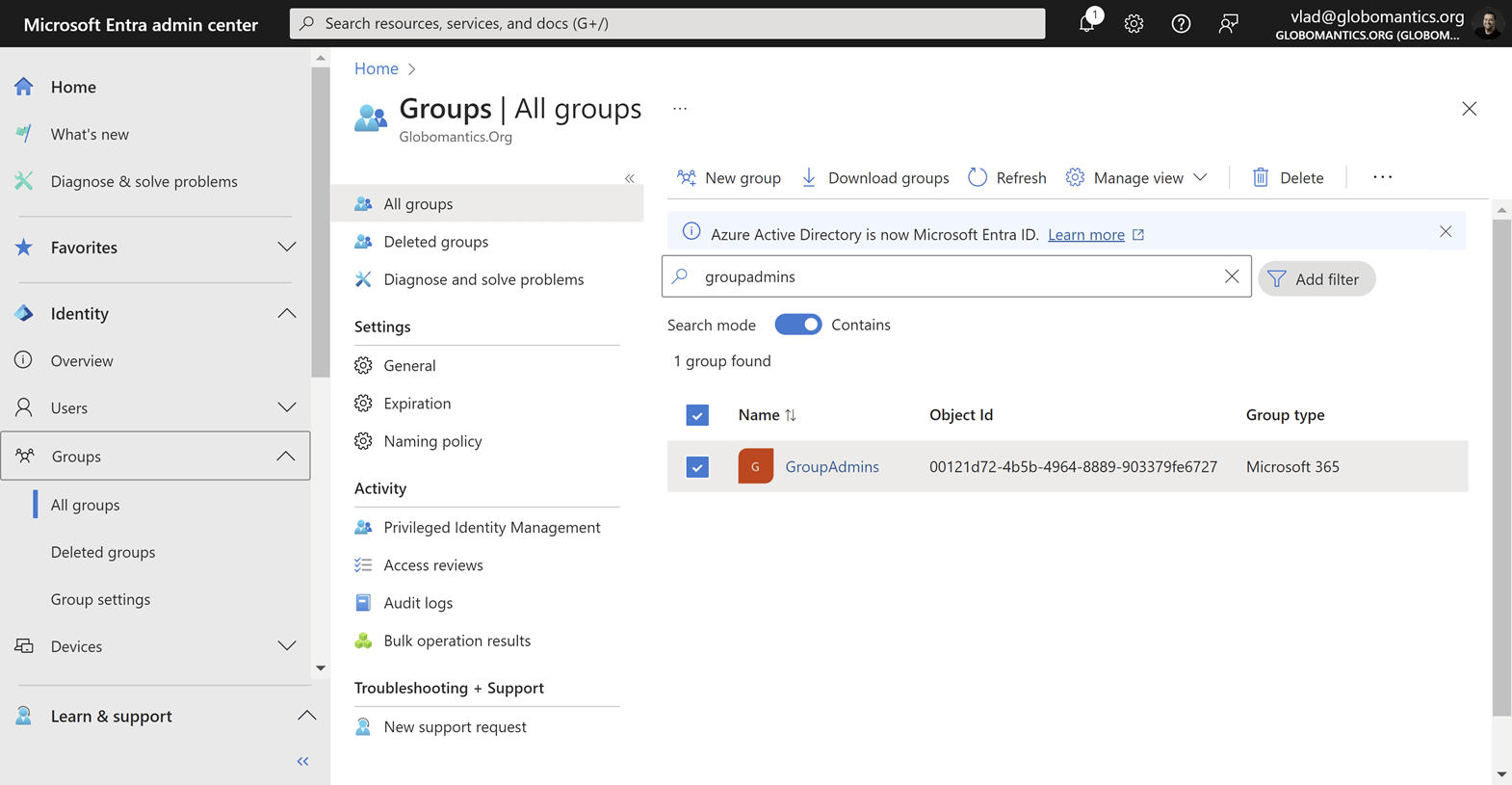
Please see the “GroupAdmins” group above, which is marked as a “Security” group: this is the group which we have created either in Entra ID within the Azure Portal, or Groups within the Microsoft 365 Admin Portal.
Limit access for creating Microsoft Teams
We are going to use that group to limit access for creating groups only to members of the “GroupAdmins” group. There is no visual setting for that, so we will need to use PowerShell for this. This requires you to have premium Entra ID licenses in your tenant, either standalone or from your Microsoft 365 E3 or E5 Subscription.
For this script, we will use the Microsoft Graph PowerShell module as well as the Microsoft Graph Beta PowerShell module so you might need to install them if you haven’t already. You can find the full instructions on Microsoft Learn over here.
Install-Module Microsoft.Graph
Install-Module Microsoft.Graph.BetaWe will then need to connect to the Microsoft Graph with the following cmdlet! You will be prompted for your username and password and the second authentication method if configured.
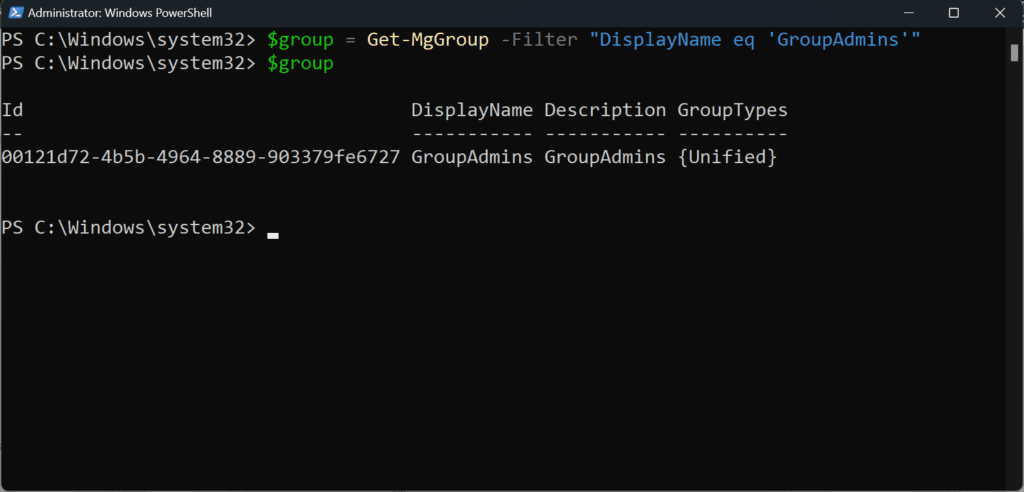
Connect-MgGraph -Scopes "Directory.ReadWrite.All", "Group.Read.All"Next up, we need to save our GroupAdmins group in a variable, as we will need:
$group = Get-MgGroup -Filter "DisplayName eq 'GroupAdmins'" +You can output the $group variable as seen in the screenshot below, and if the PowerShell script doesn’t return anything, double-check the group name.
Using Entra ID Directory templates
To start, we are going to use Entra ID Directory templates. You can configure different Entra ID options using Directory templates. Two of those templates – “Group.Unified” and “Group.Unified.Guest” are meant to work with the Groups within Entra ID.
So, we are going to use the “Group. Unified” template to create a new Entra ID Directory Setting based on that template, limiting the group creation capabilities only to the members of our “GroupAdmins” group.
It is a good idea to first check if a setting based on the “Group.Unified” Directory template already exists there, and to see if that setting may already contain some of the values which indicate that the group creation has been limited.
Just run the following script, and if you see values like in the screenshot below, it means that your directory setting already exists.
$Setting = Get-MgBetaDirectorySetting | where-object {$_.displayname -eq 'Group.Unified'}
$Setting.Values 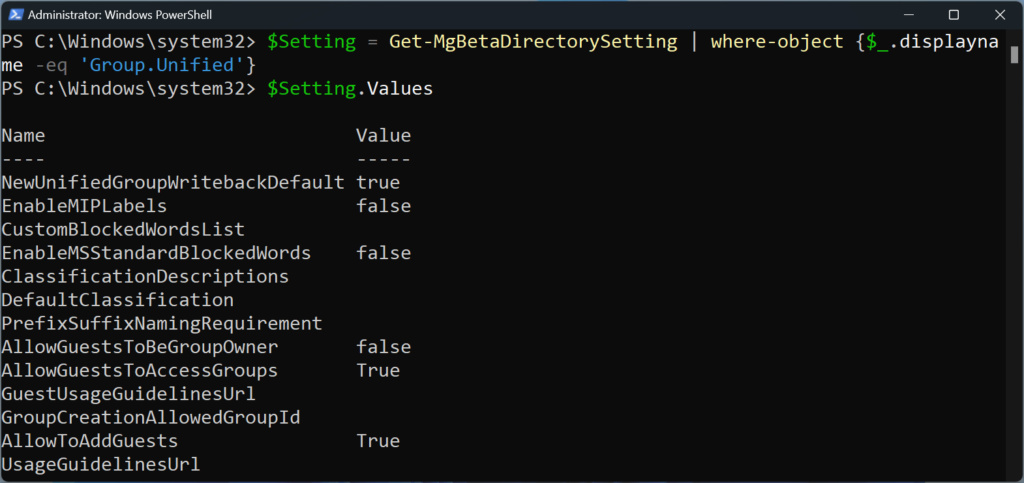
If the script above returns nothing, you will need to create a directory setting with the following script.
$SettingTemplate = Get-MgBetaDirectorySettingTemplate | where {$_.DisplayName -eq 'Group.Unified'}
New-MgBetaDirectorySetting -TemplateId $SettingTemplate.IdDisabling Microsoft 365 Groups and Microsoft Teams creation
With our directory setting created, it’s time to configure our tenant to only allow members in the GroupAdmins group to create teams. Here is the script, and I will explain it right after:
$group = Get-MgGroup -Filter "DisplayName eq 'GroupAdmins'"
Get the Group ID and use it in the “Value” of the GroupCreationAllowedGroupId below
$params = @{
Values = @(
@{
Name = "EnableGroupCreation"
Value = "false"
}
@{
Name = "GroupCreationAllowedGroupId"
Value = "<GroupID>"
}
)
}
$Setting = Get-MgBetaDirectorySetting | where-object {$_.displayname -eq 'Group.Unified'}
Update-MgBetaDirectorySetting -DirectorySettingId $Setting.id -BodyParameter $paramsHere’s a breakdown of what each part does:
- $group = Get-MgGroup -Filter “DisplayName eq ‘GroupAdmins'”: This line retrieves the Microsoft 365 group with the display name ‘GroupAdmins’ and assigns it to the variable $group.
- The $params block is creating a hashtable with two key-value pairs. These pairs are:
- EnableGroupCreation set to false: This means that group creation is disabled.
- GroupCreationAllowedGroupId set to a specific GUID: This means that only the group with this specific GUID is allowed to create new groups.
- $Setting = Get-MgBetaDirectorySetting | where-object {$_.displayname -eq ‘Group.Unified’}: This line retrieves the directory setting with the display name ‘Group.Unified’ and assigns it to the variable $Setting.
- Update-MgBetaDirectorySetting -DirectorySettingId $Setting.id -BodyParameter $params: This line updates the directory setting identified by $Setting.id with the parameters defined in $params.
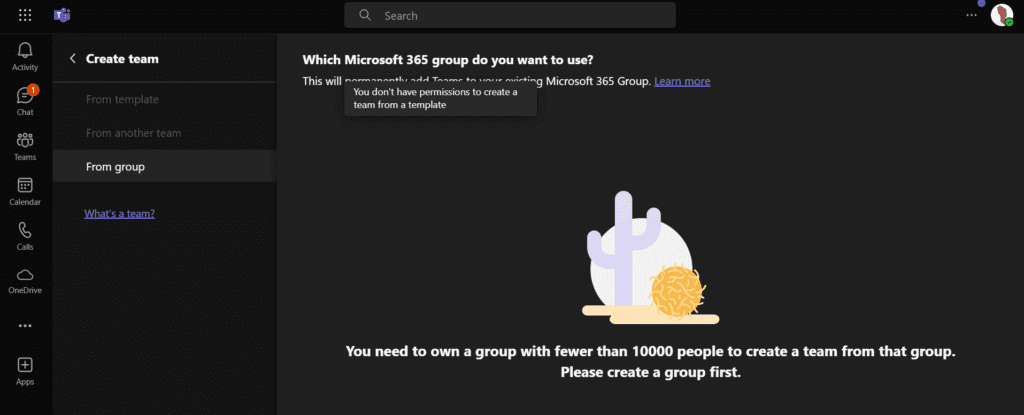
Testing Microsoft Teams permissions limits
So, let’s try to create a team now with a user who’s not a member of the abovementioned group. While that user will still see the “Create team” button for the next 30-60 minutes (it takes some time for Teams to propagate those settings from Entra ID), the button will soon either disappear in places such as Outlook or be disabled and the user won’t be able to create groups (and new Teams) anymore. However, they are still able to add Teams for existing Microsoft 365 Groups they are an owner of.
Now that we have configured this setting, you should consider setting up a Microsoft Teams provisioning solution that would include requests, approvals, and creation.