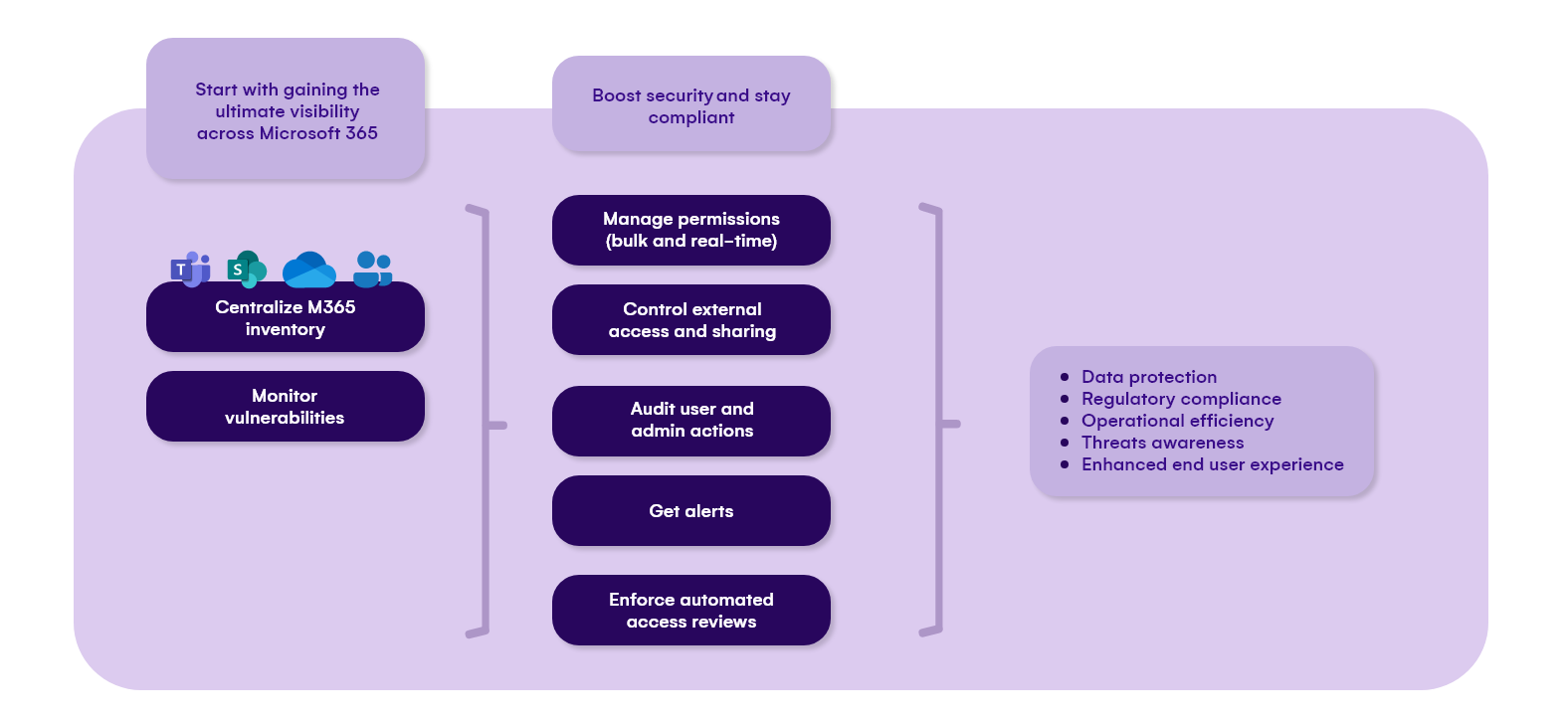
Enhance the security of your Microsoft 365 tenant
Complete overview of permissions, sharing and user actions. Take necessary actions to prevent security problems and data leaks, stay compliant with regulations and keep the data secured in your environment.
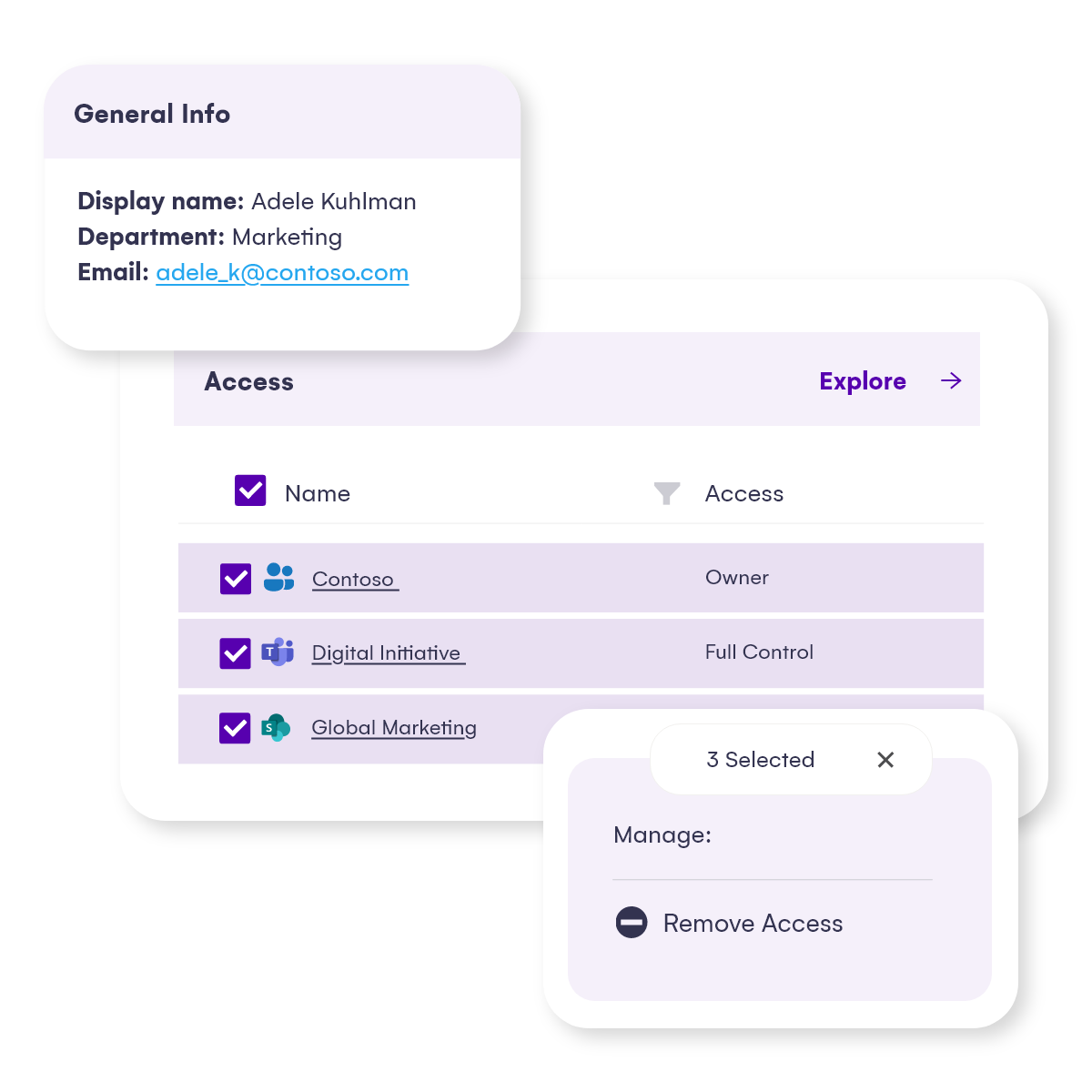
Who has access to what in Microsoft 365 – find all crucial information instantly
Cloud collaboration improves productivity, but data can easily be exposed to wrong people. Also, when a person leaves or switches department admins need to react fast and transfer or remove permissions for multiple workspaces.
- Explore permissions down to the file level. Stay ahead of security issues with real-time updates.
- Easily manage memberships, sharing and permissions in bulk across Microsoft 365 workspaces.
Being able to get all the information quickly in a centralized place and perform powerful actions helps admins to prevent security problems.
Control external access and excessive sharing
Uncontrolled external sharing is a big threat for your data safety. The inability to restrict external access to your confidential data may result in unauthorized use while detecting all sharing links may take hours of using PowerShell scripts.
Get complete clarity with Syskit Point – find and manage external and guest users, shared content, and sharing links.
Ensure secure collaboration, avoid data leaks and make sure that only the right people can access sensitive data.

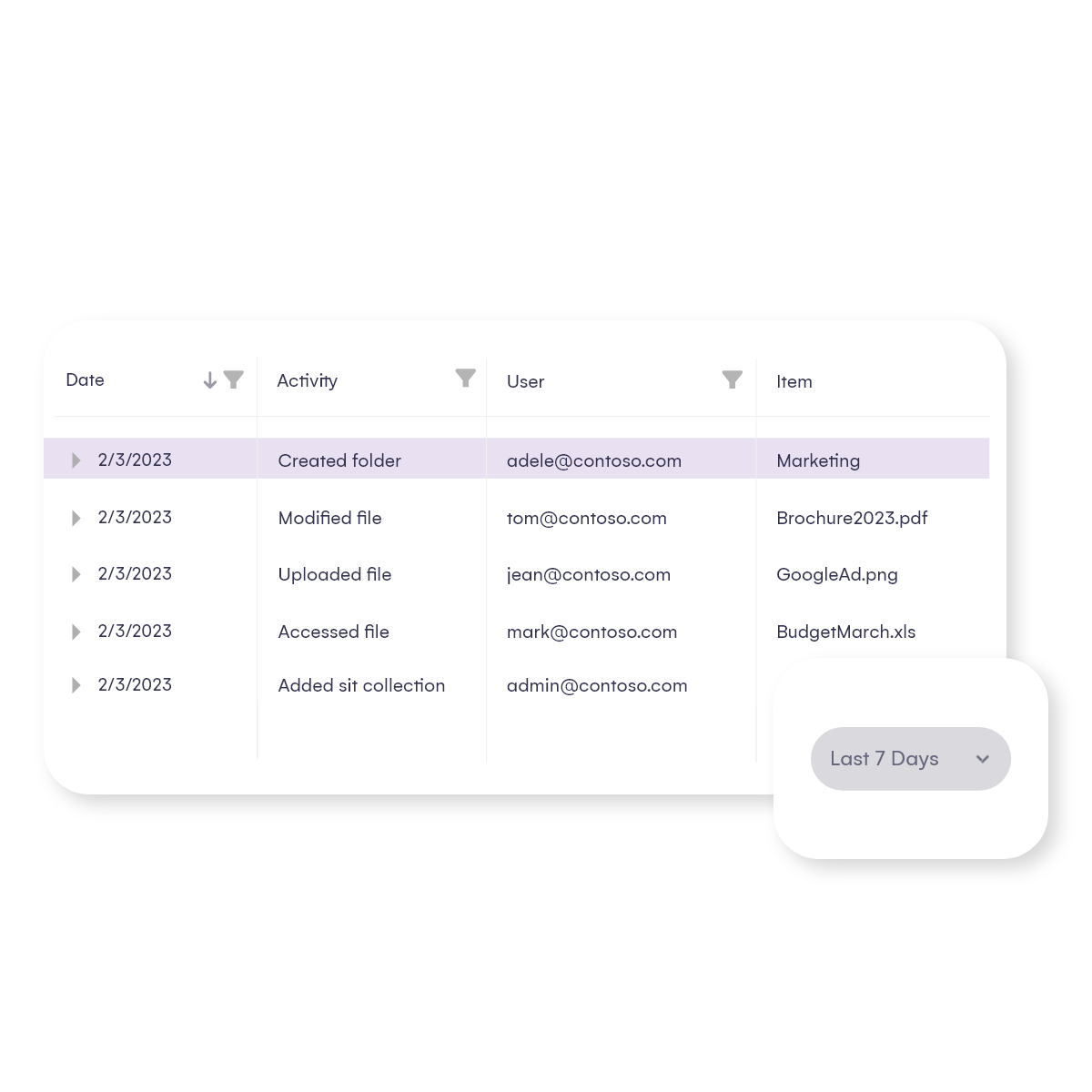
Auditing across Microsoft 365 – detection, prevention, compliance
It takes a lot of time to get to the bottom of who is behind a security breach, suspicious activity, or a permission change.
Boost security by being able to easily detect every user and admin activity and quickly prevent malicious actions across your Microsoft 365 environment.
Have the tools you need to stay compliant with ever-changing regulations with centralized visibility across all logs.
Be aware of your M365 health – stay compliant and keep it secured
Discover the most critical vulnerabilities and misalignments with Microsoft 365 best practices. Set up automated actions to keep your environment secure and under control in real time.
Proactively detect suspicious
actions with alerts
Receive proactive notifications directly to your email – for example, when a suspicious user action or sharing is detected. Customize alerts, react promptly, and keep your environment secure.
Control access with policies and regular reviews
Access only for the right people is crucial – by enforcing automated access review requests you can be sure that this is checked regularly! Delegate responsibility from IT team to owners, who have operational knowledge of who should have access to their resources.

Trusted by










Contact us
Get in touch to find out how Syskit can help you govern your Microsoft 365 estate


