Dealing with unique SharePoint permissions in Office 365
Table of contents
Each time you share a specific folder or file, rather than the entire site, you create an exception called unique permissions. As time goes by, the increasing number of unique permissions requires additional administration as it becomes harder to govern them. If you don’t adequately regulate unique SharePoint permissions, onboarding and offboarding users or managing collaboration with external vendors may give you a headache.
How do permissions in SharePoint work?
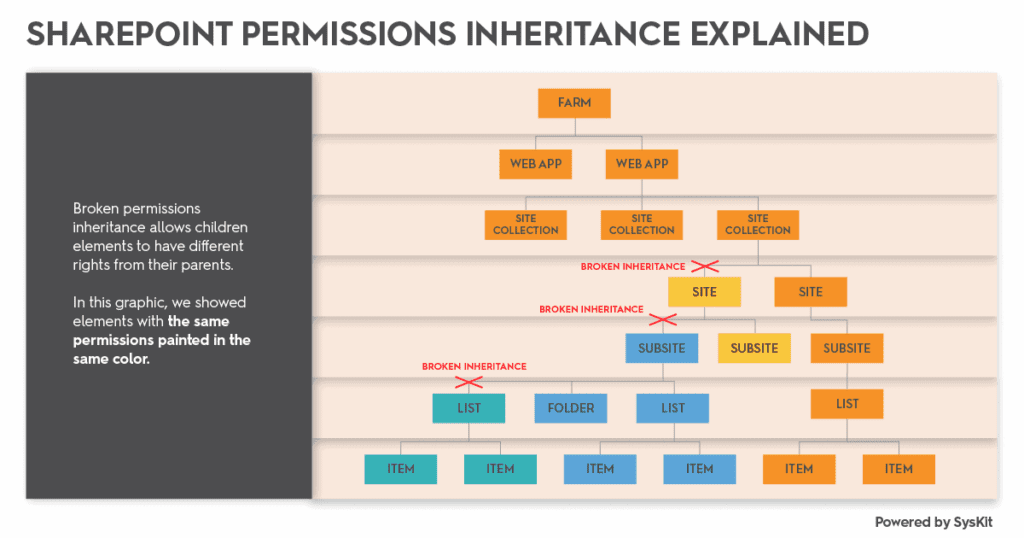
By default, all SharePoint objects inherit the permissions structure from their parent – an object on a higher level in the hierarchy. The only exceptions are “root “sites that don’t have a parent object. What does this mean in practice? Once you define your permissions structure on an Office 365 site level, all files, folders, and lists created on that site are accessible by the site users – that is, they have access to all the content on that site.
When you’re granting access to a subsite that inherits permissions from a parent, keep in mind that it gives access to all other subsites and the parent site as well. This kind of architecture is less common these days with the rise of modern sites. However, you should always be careful and double-check your security settings.
Best practices for unique SharePoint permissions
These are limits and recommendations by Microsoft on how to handle unique SharePoint permissions:
- Fifty thousand uniquely shared items per list is a hard limit defined by Microsoft. After you go over that threshold, your site will no longer work as intended.
- To maintain good site performance, keep the number of uniquely secured items under 5000 per each list/folder.
- Breaking permissions inheritance and giving unique access to multiple files makes Office 365 access and security management a cumbersome task for your administrators and owners.
- Make sure that giving unique SharePoint permissions to a specific file is an exception, not a rule.
- If you have a large number of files that have specific access requirements, consider organizing them in a dedicated list/library or even a new site.
How to report on and manage unique SharePoint permissions in Office 365?
There is no out-of-the-box report in Office 365 that will give you the list of all your content with broken permission inheritance. What is worse, there is no visual indicator that some folder or file has a unique set of permissions.
If you wish to document and report on unique SharePoint permissions, you will need to check every single subsite, library, folder, or file to ensure that the right people have the proper access to it. If you ever tried to document all your files with unique permissions, you know that we are talking about hours of manual work.
The process of checking unique SharePoint permissions is different for different levels of SharePoint objects.
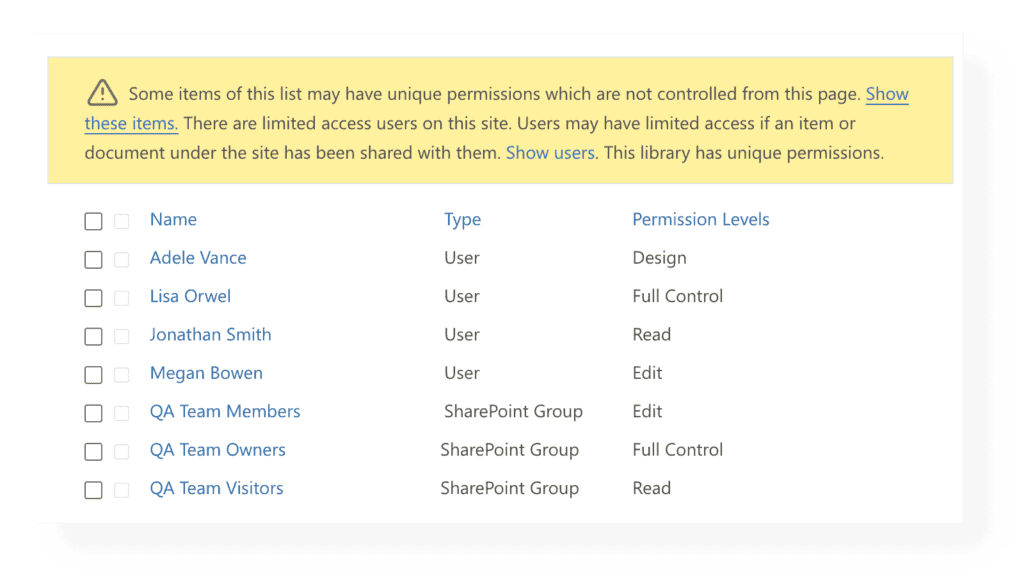
Checking the unique SharePoint permissions for a document library
- Navigate to a subsite for which you wish to audit access and check permission inheritance settings.
- Click on the gear icon in the upper right corner and select Site permissions. Select Advanced permissions settings to see permission details and inheritance status.
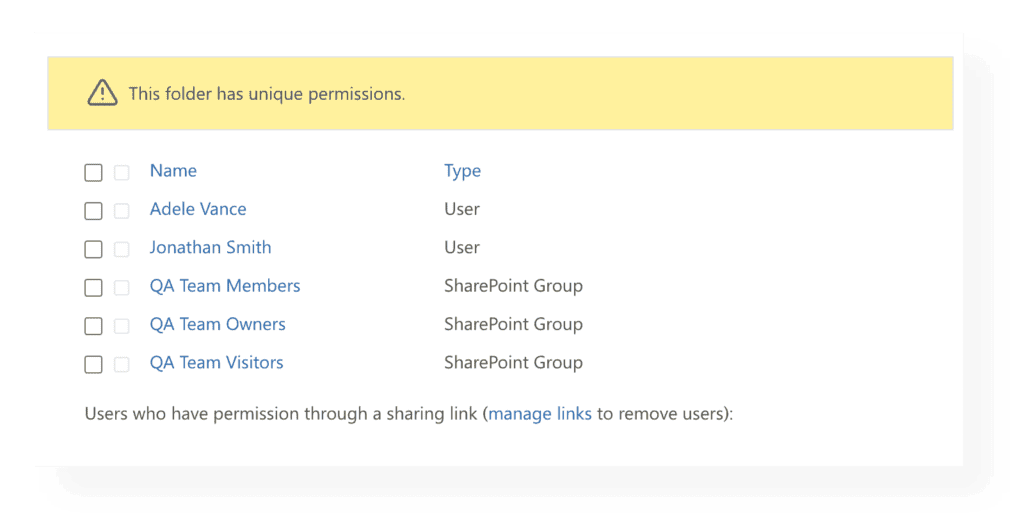
Checking the unique permissions for a folder
- Select the checkbox next to a folder for which you wish to inspect unique permissions.
- Click on the Info icon on the right-side panel.
- Drill into the Manage Access link.
- You can check access here and manage it, but click on the Advanced link if you wish to explore access in more detail.
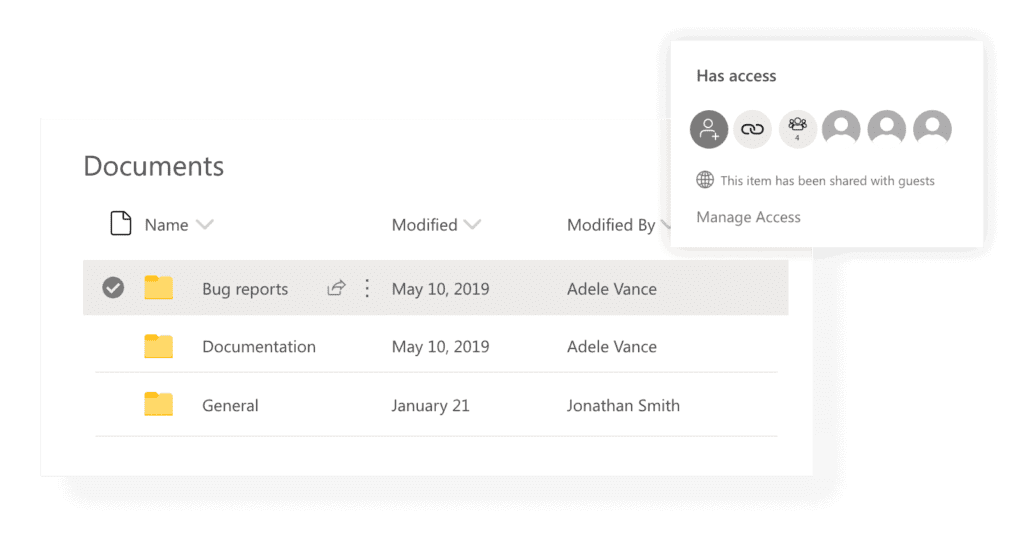
Checking the unique permissions for a file
When it comes to detecting unique permissions on the file level, follow the same instructions as for the file.
- Select the checkbox next to a file for which you wish to inspect unique permissions.
- Click on the Info icon on the right-side panel.
- Drill into the Manage Access link.
- You can check access here and manage it, but click on the Advanced link if you wish to explore access in more detail.
Creating and deleting unique permissions
Once you get to an Advanced permission screen, you can:
- Stop inheriting permissions – Use this option if you have specific access requirements for the selected object. Once you click the Stop Inheriting Permissions button, you will create a unique permission, and no permission change at that level or below will affect the parent. However, the changes will be propagated to child objects which still inherit permissions. Remember that SharePoint groups are the exception because they propagate members’ access throughout all the levels of the site structure. Wherever a SharePoint group is present, members will have access to that object, even if you broke the permission inheritance on the particular object.
- Delete unique permissions and restore permission inheritance from a parent. Once you click this button, you will remove all permission changes that you did on this object and repropagate the permission and security settings from the parent.
- Document and report on unique permissions and who has access to what. If you are following best practices for securing your files and folders, you will grant access to specific users through either a SharePoint or Active Directory group, rather than directly to the object. Keep in mind that you can’t directly see who are the members of Active Directory groups that have access to an object in SharePoint. You will need to check that membership manually, which only increases the effort required to perform this task. You can use Syskit Point to see from a single report all the users who have access to an object, no matter how they got it.
Security consequences of sharing and copying link buttons in Office 365
One of the most common but also unintentional ways of how unique permissions occur in Office 365 sites and OneDrive is simply by copying or sharing a link to a file. Clicking on the Copy link or Share button, you stop the permission inheritance for that folder or a file.
It is essential to know that even after you click the Stop Sharing button on a file, you will not restore the permission inheritance. This action will remove all users except the owners, but it will not restore the parent permissions’ inheritance. This common misconception leads to chaos down the road. You will need to fix the permission inheritance in the situation mentioned above manually.
If you don’t wish to break inheritance every time you share a file with your team members, it is recommended to use the People with existing access option. That type of link will not break the permission inheritance.
Minimizing the risk
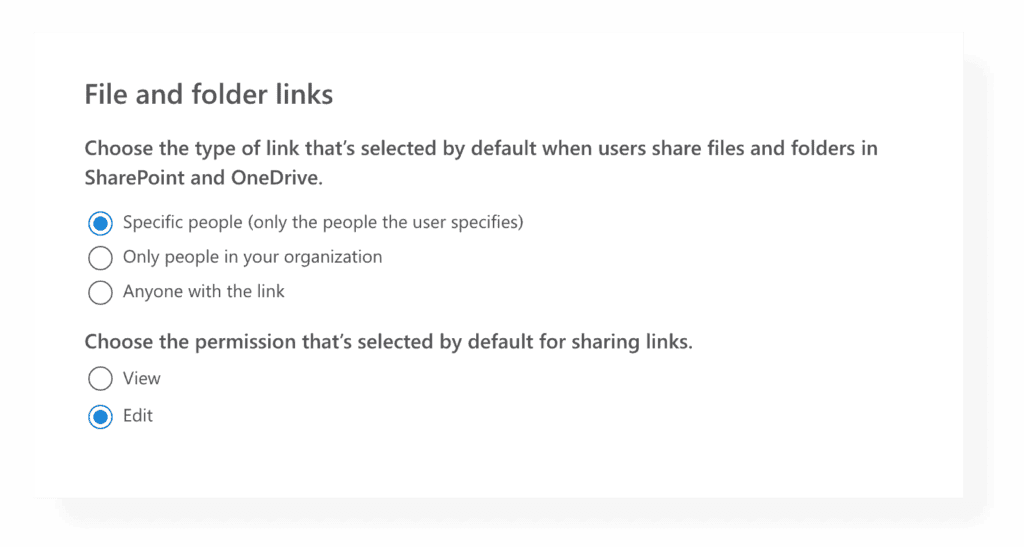
It is especially important to set the proper default settings for the sharing links to ensure that copying a link does not provoke a security risk.
Navigate to the SharePoint Online admin center- > Policies -> Sharing and choose which option should be the default for your company to mitigate risk to a minimum level.
How can Syskit Point help you keep control over sharing and unique SharePoint permissions?
Syskit Point continuously crawls your entire Office 365 environment. It offers a wide range of permission reports to detect potential security risks in a highly visual, reliable, and fast way.
There is no need for any manual work, and all the access information is regularly updated. That way, you always know who has access to what and, most importantly, it saves you hours of manual work.
Visual Indicators
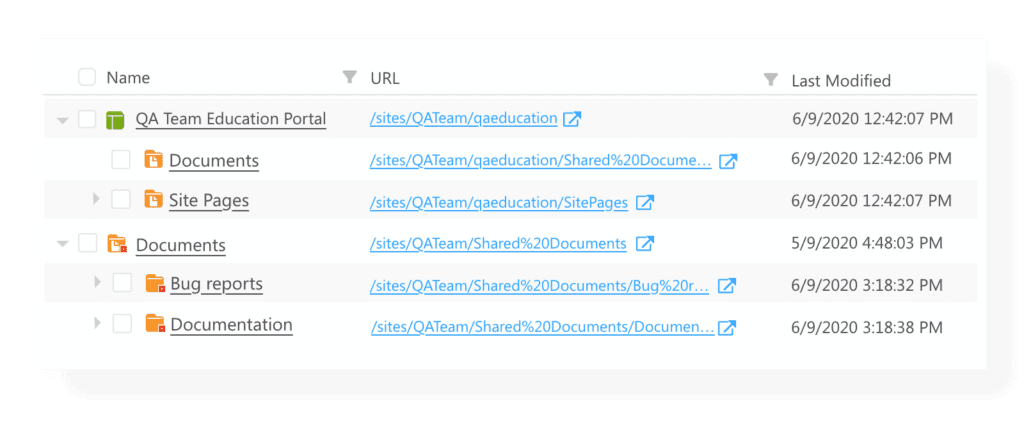
Whenever you are using Syskit Point to manage access and content across your teams, groups, and sites, it will indicate with a little red square if objects have unique permissions.
Keeping track and managing unique SharePoint permissions
By using the Details Screen for an Office 365 group, team, or a site in Syskit Point you can easily monitor how many items with unique permissions you have.
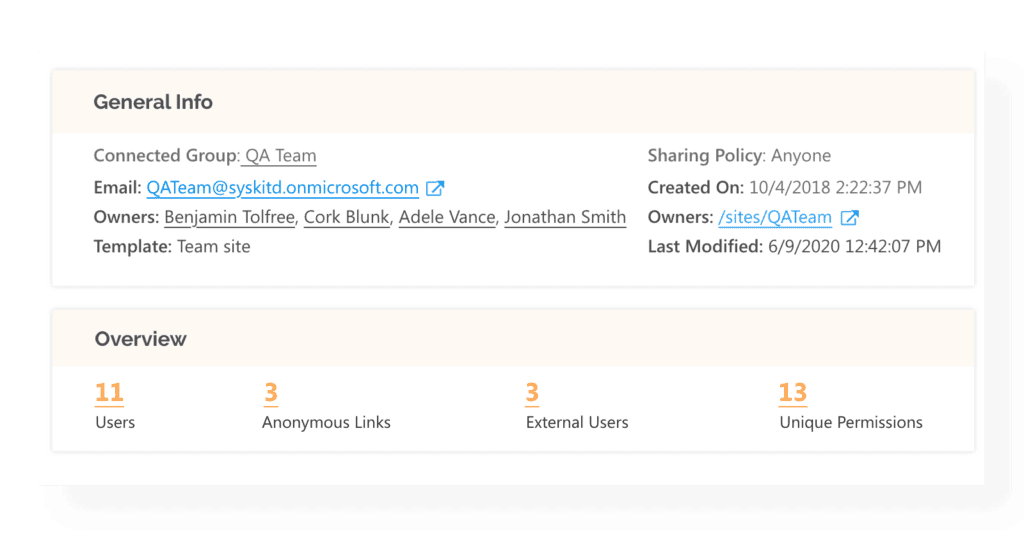
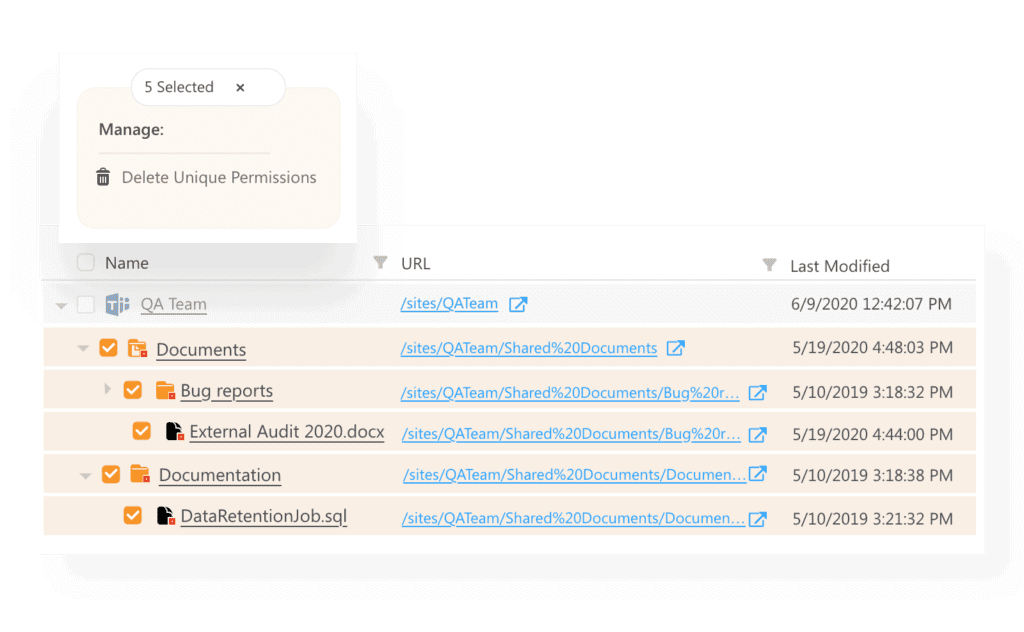
Drilling into that number of items with unique SharePoint permissions, you get a complete overview of sites, libraries, files, and folders that require your attention and differ from the parent’s permission. This report is called Unique Permissions and for that single team, group and site it will:
- Enable you to restore the inheritance for multiple files in bulk immediately.
- If you have the audit feature enabled, it will provide you with the info of who and when this file was initially shared, making it easy for you to check if that is valid or not.
Bulk reporting on Unique SharePoint Permissions
If you wish to report on unique SharePoint permissions for multiple groups, teams, and sites, use Syskit Point’s global report called Unique Permissions. Navigate to the Reports section of the tool, choose the Unique Permissions report, and select all the resources that interest you. Syskit Point will generate a detailed Office 365 report containing all detected unique SharePoint permissions in a matter of minutes.
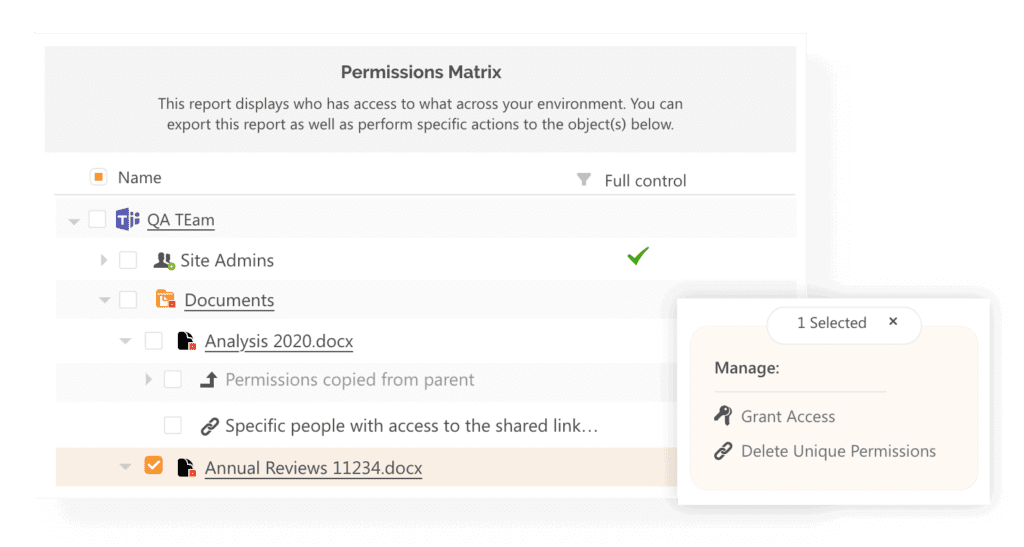
Permissions Matrix
If you wish to know who has access to those uniquely secured files, use the Permissions Matrix report. It will tell you all the places where unique SharePoint permissions occur and give you a detailed overview of all users, SharePoint, Active Directory, and Office 365 groups that have access to it. Besides that, you can immediately see the members of all those groups in the same place.
Syskit Point also can show you only the permissions that differ from the parent, making it much easier for you to keep track of permission changes and ensure a high level of security.
Multiple Office 365 access editing actions are available directly on this report, and as soon as you execute them, Syskit Point will show you the new permission status in real-time.
- remove unwanted access
- stop or restore permission inheritance
- sharing links management
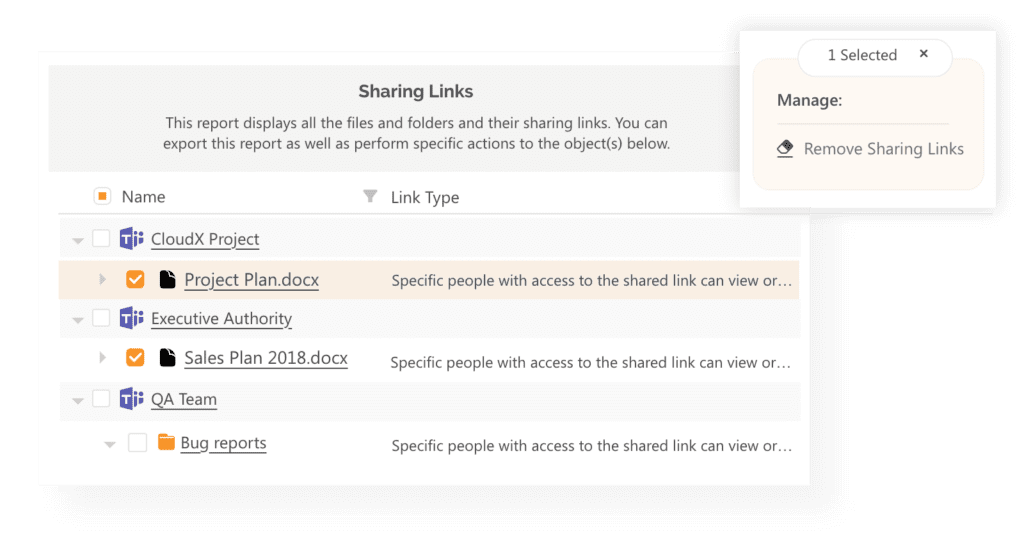
Sharing Links Report
If you want to check all the sharing links your users and colleagues created, there is an easy and intuitive way to do it using Syskit Point.
When running the Sharing Links report, you get to choose which types of links interest you:
- Share with specific people
- Anonymous links
- Company-wide links
The report provides detailed info on all the types of links created on your team or group site:
- who created the link
- is it a view or edit type of link
- who can use this link
- the creation and expiration date
You can remove the multiple links shared with specific people at once.
Conclusion
Sharing and breaking permission inheritance on your content is a powerful Office 365 collaboration tool that can make your life easier. However, if you don’t understand the security and administration implications of unique SharePoint permissions, keeping track of who can access what can quickly turn into your worst nightmare.
Keep in mind that most data leakage incidents in Cloud environments are caused by settings misconfiguration by the end-users or inadequate management mechanisms. Always strive for complete transparency in your Office 365 environment and regularly report and review who has access to what.


