So, you want to be an IT admin? Here’s your starter kit.
Table of contents
Ensuring complex environments and company knowledge are protected is no small task. And although security as such isn’t the core responsibility of IT admins, they are required, now more than ever, to be able to think and act like security experts.
Saying IT admins don’t have to know much about security would be like saying a professional fighter doesn’t need to understand the business side of their sport.
So, if you are trying to stop the relentless flurry of security leaks that businesses face, or you’re trying to become an IT admin in general, here is a starter kit of five types of arts you need in your tool bag to stay on top:
- Cloud infrastructure security
- Microsoft 365 security and communication
- Governance automation
- Monitoring
- Access management
All five are helpful, all five are practical, and all five can be completely unnecessary.
Cloud infrastructure security
People understand hackers are a threat. They are almost mainstream. But what people often fail to understand is the fact that, according to IBM, 95% of cyber security breaches result from human error. That means that actual security vulnerabilities don’t cause modern breaches and that no one has to hack you in a traditional sense to steal your data.
That theory supports the Impacts of digital transformation on IT admin’s report, confirming that 40% of IT admins reported a data leak in the last year and that one in four IT admins believe their non-tech colleagues don’t have enough skills to follow the security policies set by the company.
Since IT admins are typically the ones who configure cloud infrastructure security, understanding all mentioned above and having a plan for managing those risks is a crucial skill for everyone working as one.
Game changer
One doesn’t actually need to be a cloud infrastructure security expert to be a good IT admin. Hear us out.
One can stay aware of all user activities, easily understand who has access to what, and automatically gain complete visibility over their tenant without spending days configuring cloud infrastructure security.
Syskit Point, a platform for visibility, management, and governance for Microsoft 365, can integrate with one’s M365 infrastructure and provide a comprehensive understanding of their surroundings.
How does it work?
Initially, the crawler connects to the Microsoft Graph and SharePoint CSOM APIs, creating a full scan of the tenant’s user properties, structure, and licenses. The Graph API retrieves, while the crawlers process and enrich the data about the workloads such as Microsoft Teams, SharePoint sites, and OneDrive.
The enhanced metadata is stored for future usage in designated stores. After the initial crawl, the crawler seeks changes with the incremental crawls.
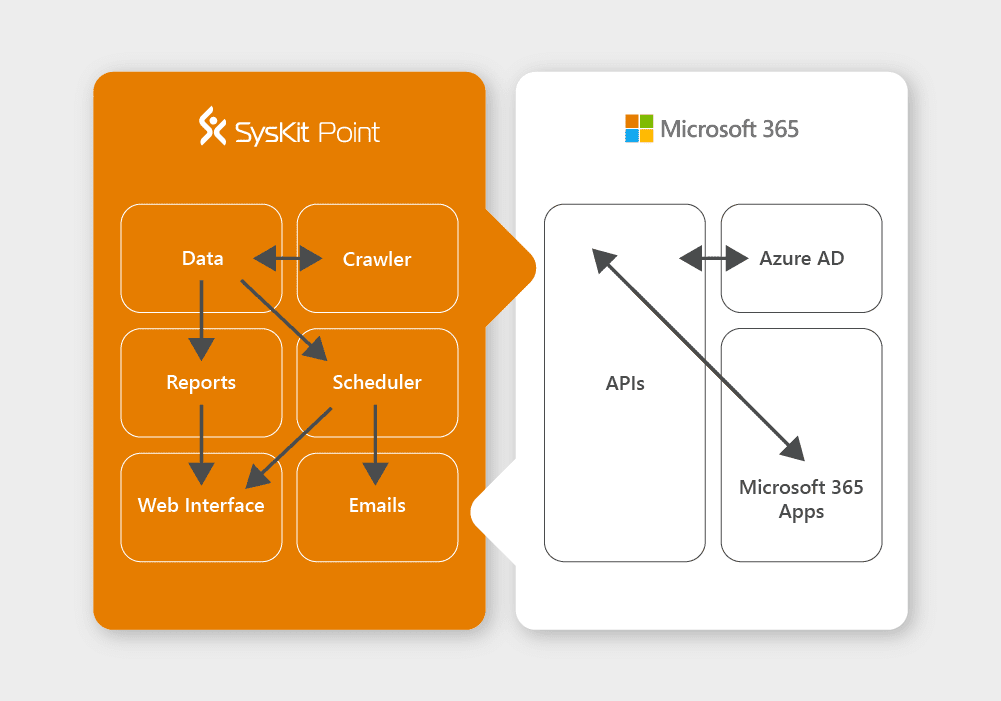
One, as an end-user, consumes the data gathered using various reports via web browsers or scheduled emails and can count on being alerted in the user interface if any policy violation happens.
Practical, right? We’ve told you so.
Moving on to the next one.
Microsoft365 security and communication
Much more so than developers, security engineers, or CISOs, IT admins are sort of referees, so to speak, between the end-users and rules that are set up.
This means that IT admins can prevent and mitigate Microsoft 365 security risks that could arise from their non-tech colleagues’ mistakes – for example, by drawing their attention to current phishing attacks, explaining to them how sharing with external users should be conducted, or emphasizing the importance of password management.
As concluded in the Impacts of digital transformation on IT admins report, 50% of IT admins consider that non-tech employees don’t know how to apply external sharing policies properly.
So, you guessed it: good communication equals user security.
Jaw-dropper enters the scene
And while by no means do we support the premise that IT admins should work in isolation, deprived of all social skills, there is a way to make the communication and knowledge transfer part more manageable, too.
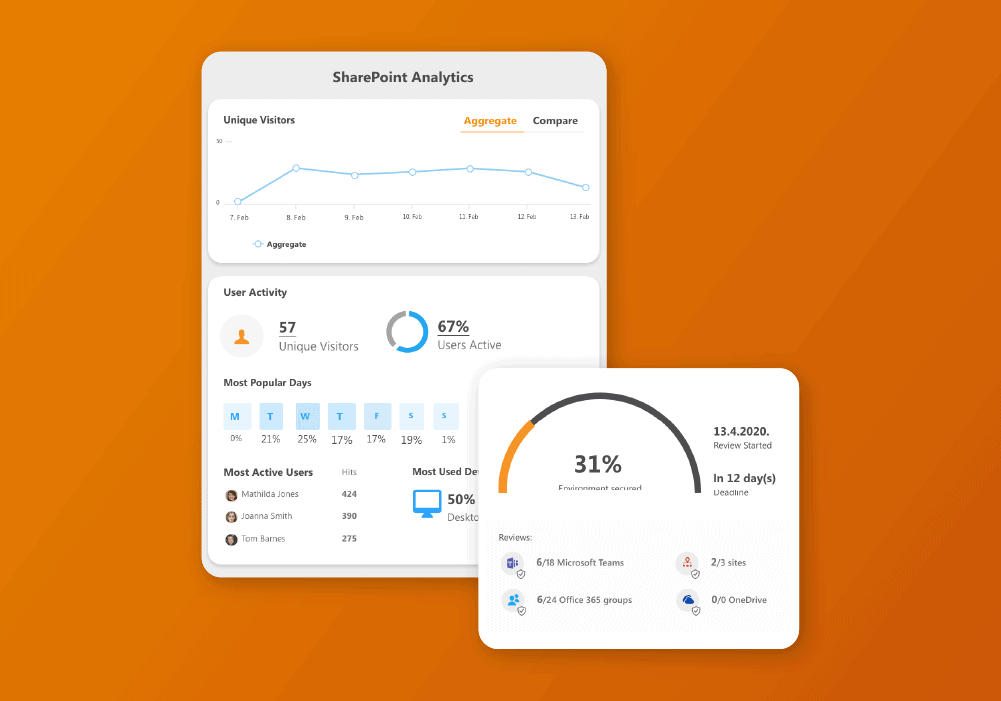
Syskit Point is designed to eliminate Microsoft 365 complexity and increase efficiency. Since 82% of IT admins deem that non-tech employees who are resource owners should be more involved in data reviews and take care of their team’s content, Syskit Point has been tailored to meet non-technical end-users’ needs.

This means that any non-technical person with a basic set of skills around the computer, like opening an email or checking their social accounts, can independently perform management actions to meet industry, Microsoft 365 security, and regulatory standards.
Seems like you really can have it all, right?
Let’s proceed to the third type of art every IT admin should master.
Governance automation
As we figured out by now, IT admins are typically burdened with tons of tasks. Many of which are repetitive. Governance automation can save hours of frustrating work by taking over tedious tasks.
Creating a script that runs every time
- an external user access files in your tenant,
- the time external users can have access to your tenant expires,
- there are changes to regulations, policies, and SOPs,
- workspace is orphaned or even
- a content sprawl happens
brings a high degree of transparency. It helps you to have continuous awareness – something every company strives for.
But it’s a sort of fine art. It takes time, patience, and practice. However…
Stance switching
Okay, now you know that scripting is good for your do more with less: less time and fewer resources assignments. But is there something more you could do when it comes to that?
The answer is: yes.
Focus on the important and automate the rest by implementing Syskit Point. It will automate your governance procedures, access, and lifecycle management and help you avoid uncontrolled sprawl in Microsoft 365 – all without you needing to spend your entire gas tank.
If you’re wondering, why should one use Syskit Point if they can write the scripts themself, here are three main reasons:
- Although it may look easy to create the first version, its maintenance is a true challenge. Microsoft changes its API with its services quite often, so one must be up to date for data to be valid and scripts to work.
- When a script collects the data from an environment, it’s a very big chance you’ll be stopped by Microsoft throttling. And trust us, you’ll want Syskit Point to deal with it instead of you.
- What’s on the inside is the most important but looks also matter. Syskit Point was created by a team of professionals that took care of everything – from the performance to the user interface attractiveness. It suits both admins and end-users.
Monitoring
With the average data breach costing $4.35 million in 2022, IT admins need to be able to spot problems before they actually happen. But how if one’s not psychic?
Some might say by enforcing protocols and educating end-users. But, as established earlier – that sometimes just isn’t enough. And Microsoft Teams, Groups, OneDrive, Power BI…all of them with their native admin centers, managing and understanding the structure, memberships, and structure is cumbersome.
Turning Point
To help you see all the blows coming your way, you need help; you need someone in your corner.
With Syskit Point, you can get the right information just when you need it and get proactive notifications straight to your inbox if:
- someone has shared a document with an external user;
- an external user has been added to a Team;
- groups privacy has changed from private to public;
- a user has logged in from outside the allowed IP range;
- Private Team or Group was made public or
- other permission changes and suspicious user activities.
With Syskit Point as your cornerman, you’ll be ready for whatever comes your way.
Access management
Part of IT admin’s security management is taking care of user accounts. Poor user account hygiene can lead to many security problems, many of which are mentioned above, but one that is often overlooked can cost like a smaller security incident.
And that is inactive licenses. The top four reasons companies overspend are
- inactive,
- underutilized,
- oversized,
- unassigned
Microsoft 365 licenses. Can you say with 100% certainty that all the licenses in your company are well utilized? If not, you should consider creating a strategy to keep track of all of them.
Or you can implement Syskit Point and let it identify mismanaged licenses to cut costs and reach the desired KPIs.
In a nutshell…
To become a successful IT admin, one must master a lot of knowledge from different fields, cybersecurity, governance, and management being just the tip of the iceberg.
But, when it comes to the last three domains, IT admins can relax if they have the fundamental skillset because Syskit Point will take care of them and help you be an ultimate admin.


