Impacts of digital transformation on IT admins report
Table of contents
We wanted to exactly find out how digital transformation impacted their work, what they think about executing governance by their non-tech colleagues, and whether they are satisfied with their tools.
The survey was conducted in November of 2022 by the research company Peekator in collaboration with Syskit. The sampling pool consisted of 205 respondents from the USA and accurately represented the targeted population.
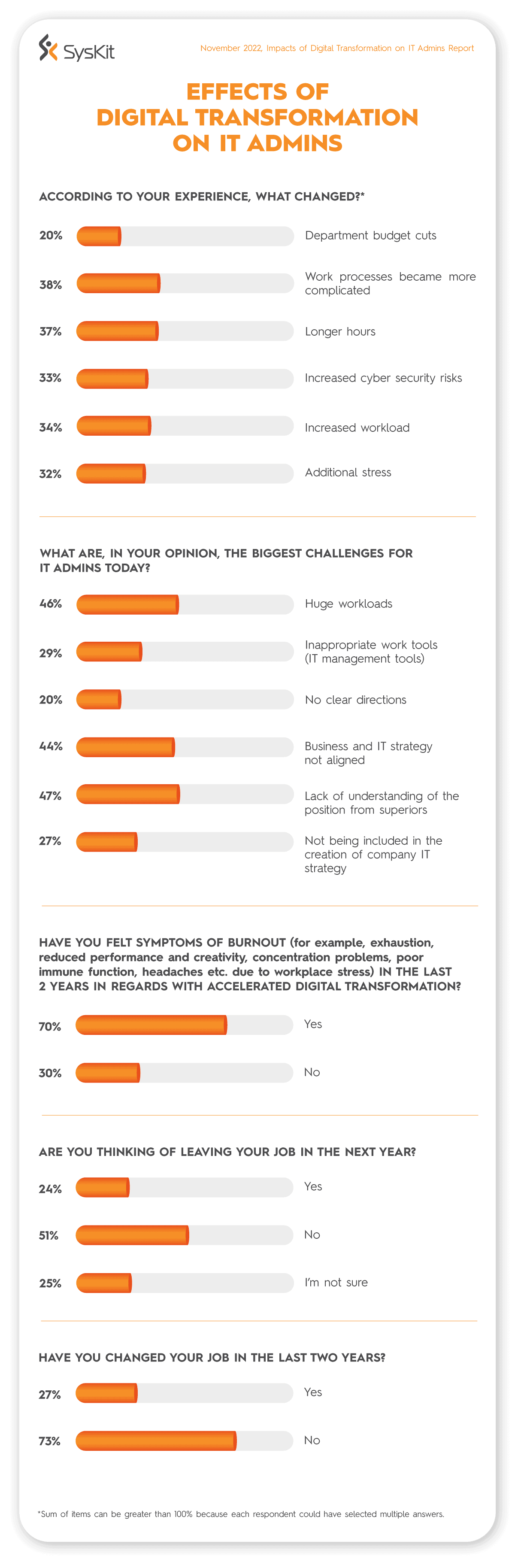
Digital transformation creates more problems for IT admins
According to IT admins, results showed the bigger the company, the more significant the impact of digital transformation. This is probably something that shouldn’t come as a surprise. Big environments, many users, more processes, and more data entailed more complex changes.
When COVID kick-started the digital transformation, many IT admins were faced with complicated migrations, transition to the cloud, the introduction of new security protocols, and the implementation of various new software.
The top three challenges during the accelerated digital transformation for IT admins were:
- work processes became more complicated (38%),
- IT admins started working longer hours (37%),
- and accordingly, their workloads have increased (34%).
The biggest challenge today: Lack of understanding from superiors
Half of the respondents consider that their main challenge today is the need for more understanding of their position from their superiors (47%), followed by huge workloads (46%), and business and IT strategies needing to be aligned (44%).
Since today’s organizations heavily depend on digital communication and processes, the fact that admins report business and IT strategy as not being aligned is concerning. A differentiated product or service is no longer enough to succeed in today’s market. Organizations must fulfill a whole array of prerequisites to stay or become successful.
Numerous business-critical tasks depend on successfully optimized IT environments, such as secure and functional collaboration, auditing and compliance, and reporting. Organizations must include IT strategists when creating an overall business strategy.
70% of IT admins felt burnout symptoms
The changes mentioned above had a massive impact on IT admins. An incredible 70% of them felt symptoms of burnout in the last two years concerning accelerated digital transformation. The answer to the serious question of how to reduce the stress and workloads of IT professionals, who are responsible for essential business operations, could lie in delegating responsibilities and implementing easy-to-use IT platforms.
Improving the availability and quality of IT tools and work conditions could also decrease turnover and curb costs connected to losing valuable staff members. One in four IT admins changed jobs in the last two years, and one in four are planning to change their job in the next year.
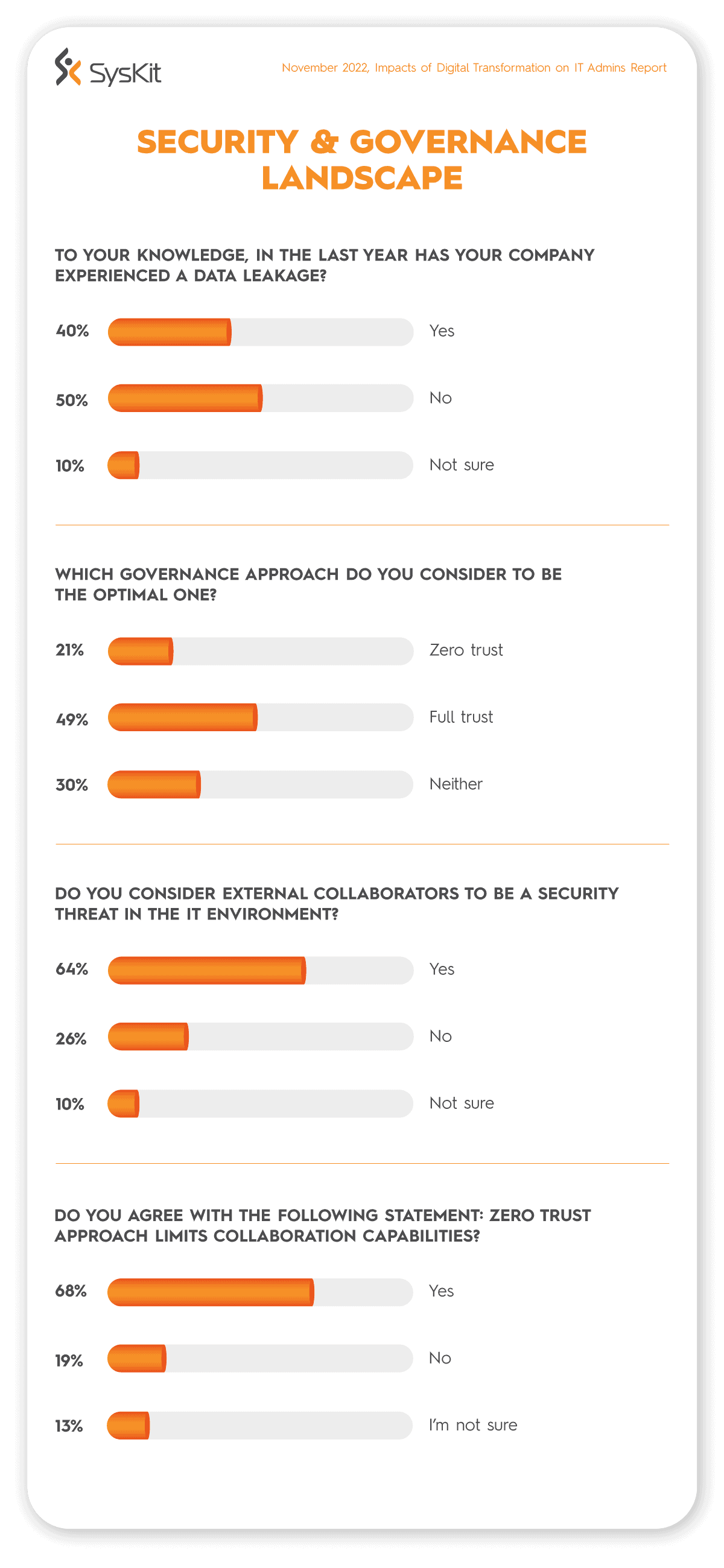
Scary security statistics: 40% of IT admins reported a data leak in the last year
The results showed that 40% of respondents reported their company experienced a data leak in the previous year. Data leaks have multifaceted costs.
Companies face:
- losing business-critical certifications
- receiving huge fines
- hurting reputation
- losing customers
- losing competitive edge
Full trust approach preferred despite its disadvantages
49% of IT admins consider the full trust approach to governance to be optimal. Although it wasn’t the topic of this survey, it is fair to presume some of the data leaks could be attributed to this approach.
The full trust approach simplifies the collaboration inside and outside of the company. It can decrease the IT admin workload by adjusting the workspace settings so that anybody in the company can create new channels, groups, or workspaces and have all the permissions usually dedicated only to managers or global admins. This is aligned with the result that most respondents (68%) deem that the zero trust approach limits collaboration capabilities.
However, this approach opens Pandora’s box where organizations’ security is based on the hope or presumption that all employees have enough cybersecurity awareness. Additionally, insider threats and risky behavior are hard to track. Without comprehensive software to track activities like changing permissions or document sharing, organizations are opening themselves to losing valuable information. Full trust increases the chances of a data leak and increases uncontrolled workspace sprawl, which encompasses the creation of duplicated and redundant data spread over the tenant. Which, in turn, impacts the functionality and speed of search and business efficiency and increases the chance of a data leak and oversharing.
So, even though IT admins consider full trust the preferred approach, the majority report that external collaborators present a security threat in their IT environment.
Zero trust, second worst
On the other hand, one in five respondents thinks that the zero trust approach is the way to go. Unfortunately, this approach also has significant drawbacks. Although some cybersecurity experts consider it a proactive approach, IT admins have to deal with endless tickets and responsibilities that could have easily been transferred to resource owners and managers.
The airtight philosophy of zero trust slows down business processes and creates more manual work for admins. Also, it limits the capabilities to collaborate with external parties. In such scenarios, to be able to conduct their work, employees turn to shadow IT under which the company has no control.
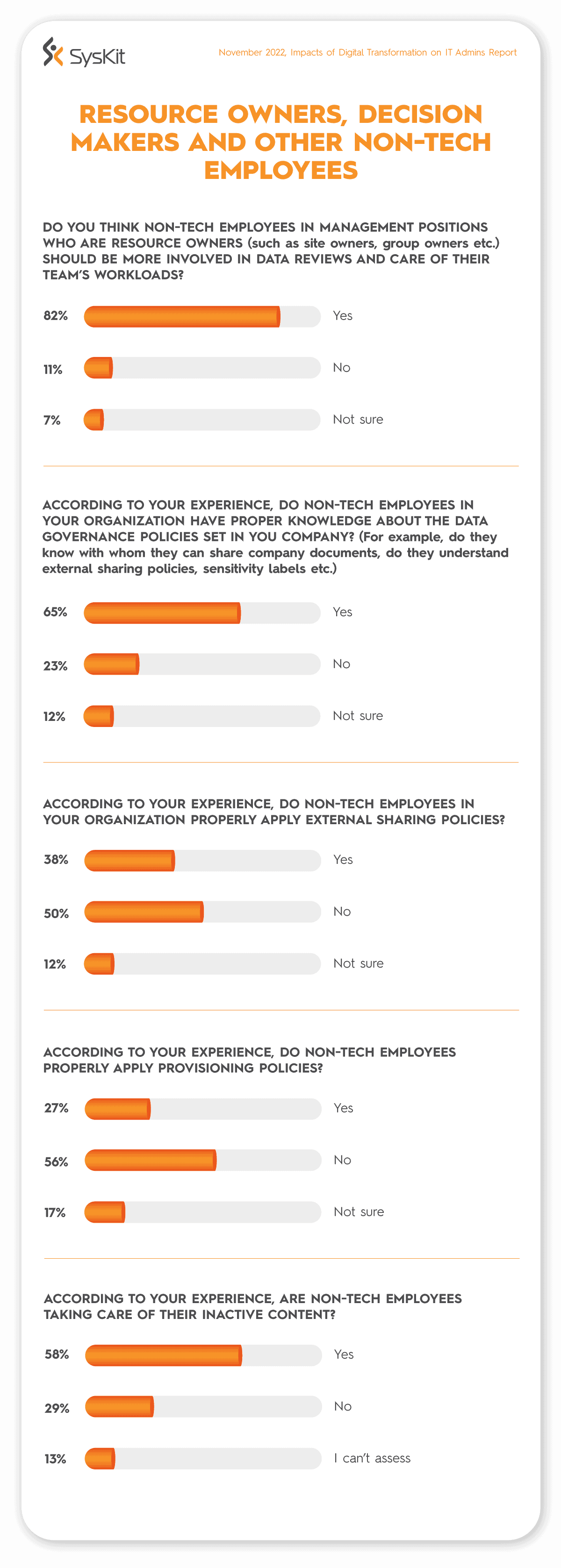
Should non-tech employees be more involved in IT processes?
The majority of IT admins (82%) deem that non-tech employees who are resource owners should be more involved in data reviews and take care of their team’s content. This would considerably help IT pros lower the workload, in keeping the tenant uncluttered and secure. For example, features like workspace provisioning can support establishing compliance from the beginning of the lifecycle and empower end-users through self-service tasks (such as requesting new workspaces).
But, to empower non-tech users to take ownership and control over their resources, they need to be knowledgeable about the subject and have the right tools to execute these tasks easily and properly. While most IT professionals (65%) believe non-tech employees have appropriate knowledge about organizational data governance policies, almost one in four IT admins believe their non-tech colleagues don’t have enough skills.
This is especially clear when asked about non-tech employee’s skills to perform specific tasks such as applying external sharing policies, provisioning new workspaces, and taking care of their inactive content.
External sharing challenges for non-tech employees
According to their experience, 50% of IT admins consider that non-tech employees don’t know how to apply external sharing policies properly. What problems does that present? For example, if a user is unfamiliar with these policies, and shares a link with an Anonymous User via an anonymous link, the organization’s control over the content stops. Those users can share content further, and the organization will have no control and visibility over those actions and won’t be able to track changes.
Suppose they share a link with an Authenticated External User with the same permissions as an internal user. In that case, the Authenticated User can abuse the given access, possibly without the permission giver’s awareness. And as we mentioned before, if a company prohibits external sharing but must collaborate externally, it is likely to have an invisible problem of Shadow IT.
Similar to External Sharing, most non-tech users don’t know how to properly apply provisioning policies (56%), and almost 30% are not taking care of their inactive content. Not taking care of the inactive content can result in workspace sprawl and unnecessary storage costs.
Tool be, or not tool be – Do IT admins have a say?
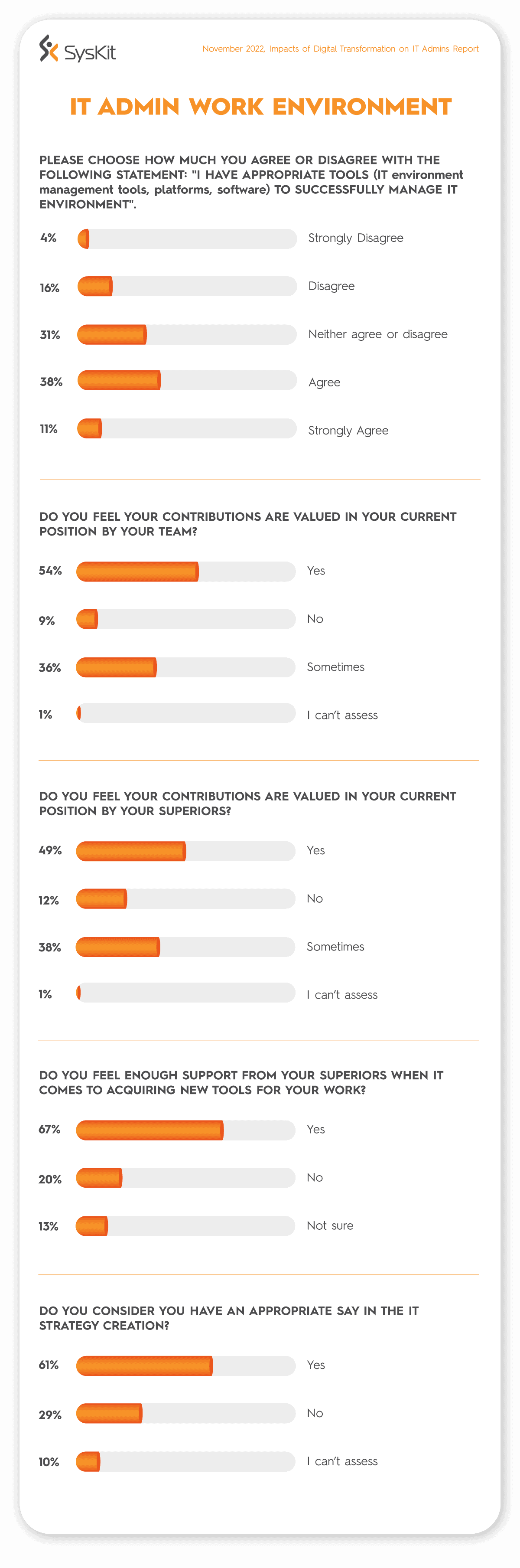
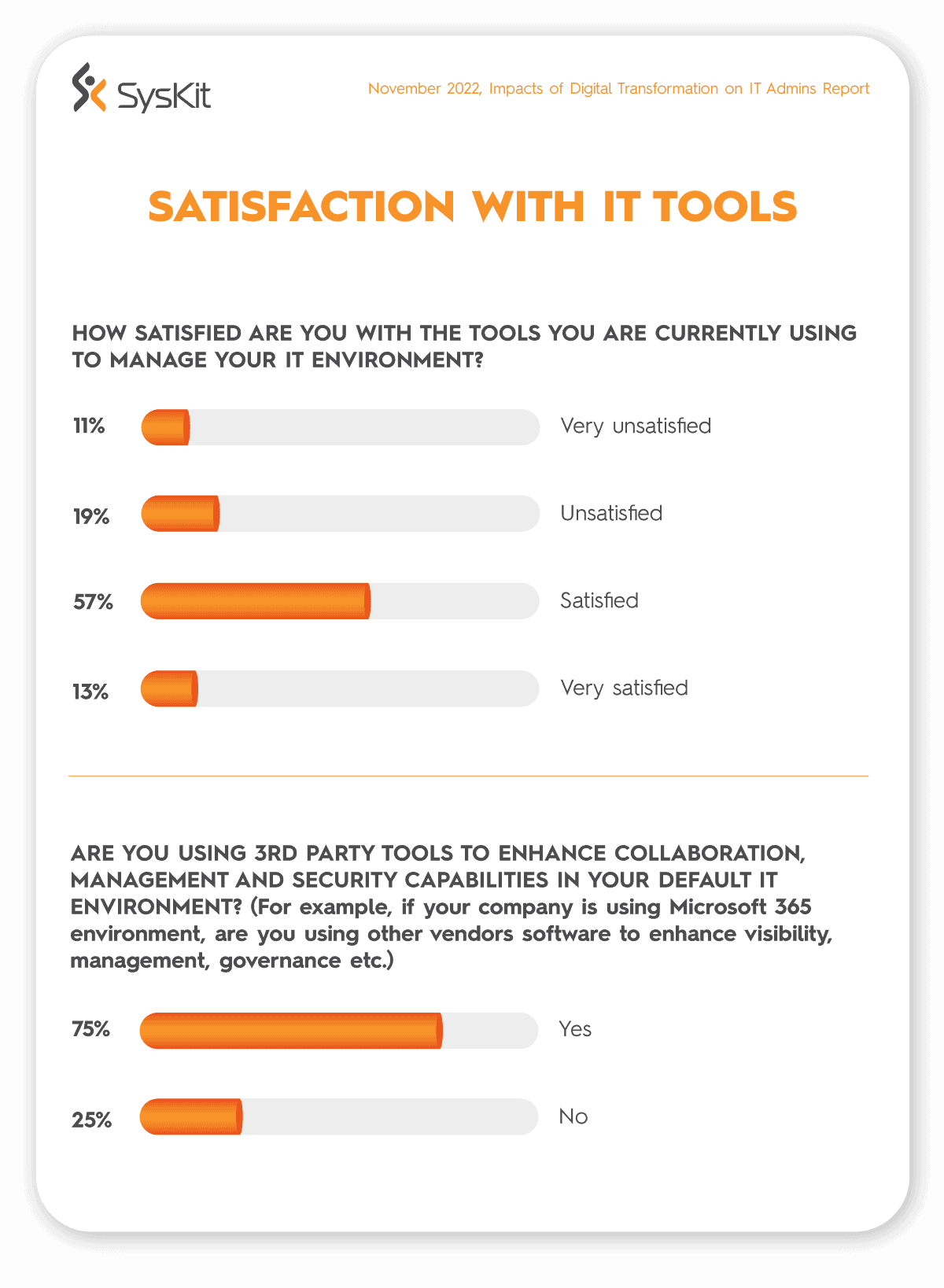
One in five respondents don’t believe they have the appropriate tools to successfully manage an organization’s IT environment. While half of them estimate they have the right tools, 31% didn’t agree or disagree.
A concerning statistic is that one in five feel they don’t have support from their managers when acquiring new work tools, while almost 30% deem they don’t have a fair say in the IT strategy. These numbers could explain part of the reason why a lot of admins consider that business and IT strategies in their companies are not aligned.
If people who manage and secure IT environments are not included in the creation of an IT strategy, it is likely that decision makers don’t have sufficient information when planning for success.
On a relatively positive note, over half of the respondents consider their contributions to be valued by their team (54%). Regarding their superiors, almost half of the respondents feel that their contributions are valued (49%).
Governance and data management awareness is on the rise
Regarding the IT tools they use to manage their tenant, almost a third of IT admins are dissatisfied (30%). Three-quarters of respondents reported using 3rd party tools to enhance visibility, management, and governance capabilities in their environments. This implies that companies have started recognizing the importance of using tools to enhance collaboration and security.
Still, the question remains: Are they using the right tools to successfully manage and secure their environment?
You can download this report as an infographic.
From Syskit’s perspective: How to make IT admins happier and data management effective
Accelerated digital transformation added to already existing data management challenges. Security and proper data governance enforcement remain significant issues for companies. The good news is that it is possible to curb frustrations for decision-makers and IT professionals and it doesn’t have to be a hassle.
By introducing visibility in the environment, automating specific processes, and centralizing management, organizations can address different IT and business difficulties. A comprehensive overview of the tenant allows organizations to take control of their resources, reduce complexities in the environment, and makes the job easier for IT admins simultaneously.
To tackle all these issues, we developed Syskit Point for Microsoft 365 environments. Our SaaS management platform provides an intuitive, easy-to-use dashboard that empowers IT admins to transfer responsibilities securely to non-tech employees.
Since team managers and resource owners have better knowledge about their workspaces, delegating responsibilities would lower their workload and decrease the possibility of error. End-users get a clearer picture of their resources and take care of their workloads through easily navigated governance and management tasks.
Syskit Point helps companies find the perfect balance between zero and full trust approaches. Enforcing data governance, applying provisioning policies, and taking care of access management, auditing, and reporting doesn’t have to be a 2023 problem. Discover Syskit Point for yourself and how it can empower your users and business right now.