How to set up governance for Microsoft Viva
Table of contents
Microsoft Viva gives employees new ways to experience, learn, engage, and work. The Employee Experience Platform (EXP) is AI-powered, and automatically discovers, organizes, and surfaces content and knowledge. This is done through four main modules:
- Viva Learning
A centralized hub containing content libraries for learning, discovering, and sharing within the workplace. These automatically present relevant material to users, giving personalized learning pathways experiences. - Viva Connections
Gives each user their own curated dashboard of activities, news, discussions. All the latest information that’s relevant to their daily work. - Viva Insights
Supports employees to be more productive and effective, while also enabling wellbeing and focus. Insights and reports help managers understand how their teams work, giving recommendations for achieving balance and boosting performance. - Viva Topics
Data sources, content and conversations are combined into Topic Pages, using AI. The combined knowledge can then be accessed in the form of Topic cards, which appear just-in-time to employees as they work across SharePoint, Outlook, and Office.
Naturally, the ability to quickly find and share all this information comes with certain governance requirements. These are configured through security and compliance settings that apply across the Microsoft 365 tenant. It’s an integrated approach. The goal is to make it harder for users to make mistakes than it is to adhere to governance requirements.
That’s why we should first establish some Microsoft 365 governance ground rules. These can then apply to Microsoft Viva. Microsoft MVP, Susan Hanley, has some great tips you can check out below.
So let’s start with the foundations.
Microsoft 365 foundations for Microsoft Viva governance
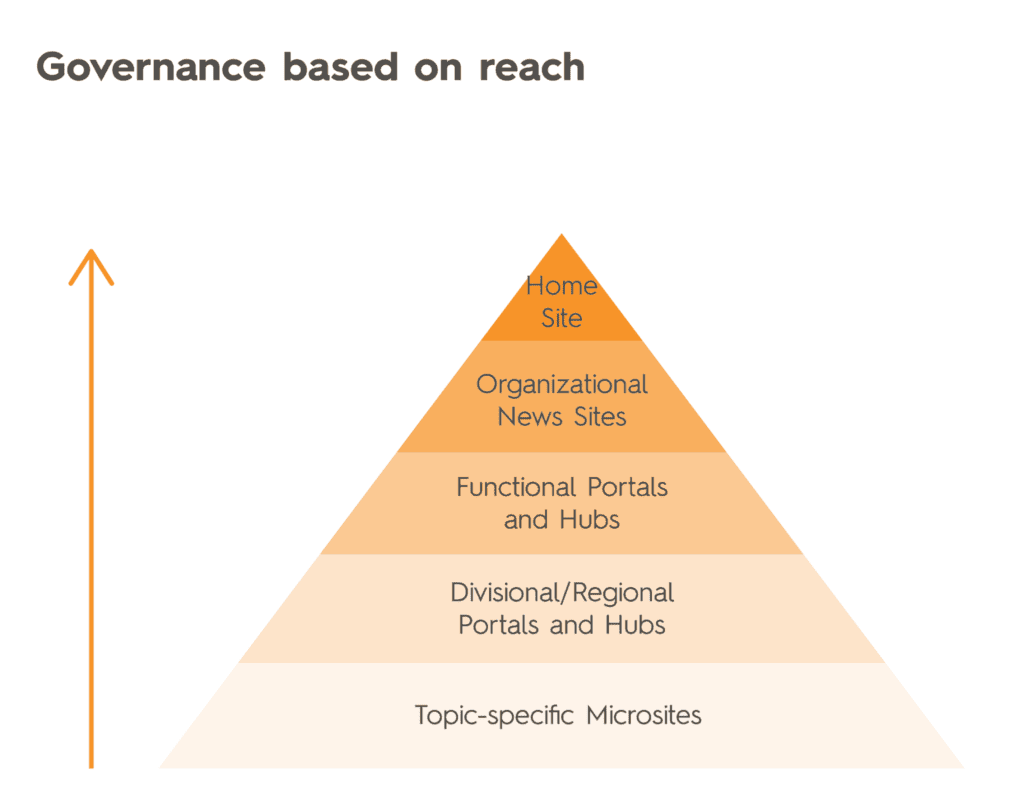
Of course, content needs different levels of governance, depending on the size of the audience. The bigger the reach, for example a home site, the more governance you’ll have to factor in. Whereas topic-specific microsites will have a smaller audience.
It’s a three-stage process.
Planning Microsoft 365 governance
First of all, put together a small team. Ideally with representation across the organization. That way ownership is shared, encouraging adoption among employees, while uniting departments ranging from HR, communications, and IT. Start by asking questions such as, “What needs to be governed?”
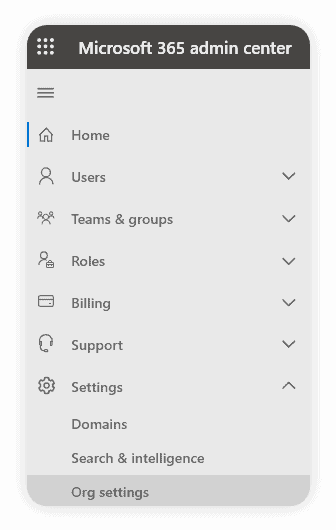
To help support and encourage collaboration, make them the first to test out new Microsoft 365 features that impact governance. For example, trialing new features that may affect how sensitive data is accessed on remote devices. Go to the Microsoft 365 Admin Center > Settings > Org Settings:
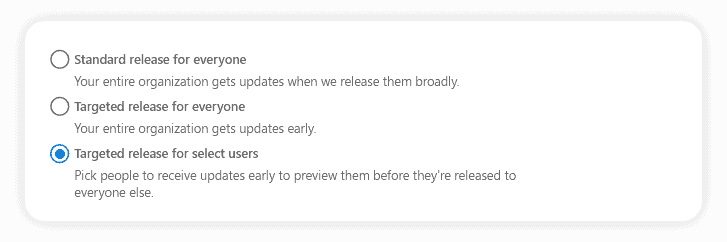
Choose the Targeted release for select users option. They can be part of the Semi-Annual Enterprise Channel.
Further topics for the team to discuss can include:
Provisioning groups for governance
Admins (with either Azure AD Premium or Azure AD Basic EDU licenses) can limit group creation by end users. However, this restricts the creation of groups in all M365 services. For example, in Yammer there will be no “Create a community” option. In Teams, the “Create a team” button will be replaced by “Create team from a group” – where users can only create teams from existing groups.
You might not want this. As a solution, Microsoft suggests asking users to complete a training course if there are concerns over governance of group creation. However, maybe you prefer to automate governance and security of provisioning. That’s when you can use a third-party Microsoft 365 tool such as Syskit Point.
Naming conventions for governance
Make a list of specific terms that should be used for governance and training documentation. If users can create groups, decide whether to set a naming policy to maintain consistency and block certain words being used. While limiting profanity is a common use case, it’s also a powerful governance tool. For example, blocking the use of “CEO” to prevent possible impersonations within published content.
First, you’ll need the Azure AD Premium P1 license. Then head to the Azure Active Directory admin center > Azure Active Directory > Groups > Naming policy:
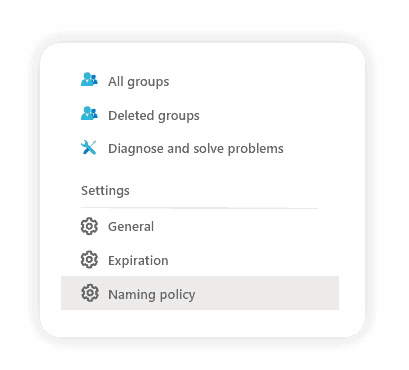
You can either add/remove terms (up to 5,000) or upload a .csv file.
Guest access and Identity Governance
Admins (with a Premium P2 license) can use Azure AD to create periodic reviews of user access to groups and applications. Sign in to Azure and open the Identity Governance page. Click Access reviews:
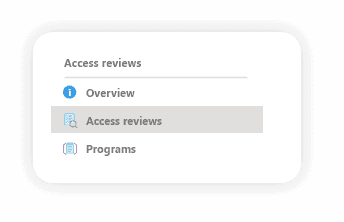
Click New access review to create recurring reviews of:
- All Microsoft 365 Groups with guest users
- Select Teams & Groups
You can define whether to review guest user access in a directory or all user objects related to the resource. You can also specify who owns the review, ranging from group owners to users or their managers. When the review is finished, you can create automated responses to save time. For example, removing denied users access, blocking sign-ins for 30 days before removing access, approving or not changing access.
Enabling information barriers for internal access
You may have legal or regulatory requirements to control information sharing between internal groups. For example, preventing merger and acquisition teams sharing information that could lead to insider trading accusations. That’s when you can make use of information barriers. These policies control communication and collaboration within Teams, SharePoint, and OneDrive.
To get started you’ll need specific licenses and permissions. You’ll also need knowledge of Microsoft PowerShell to configure the information barriers. You can then:
- Identify segments
Decide which user segments need information barrier policies. Users can only be added to one segment, which will only have one information barrier. - Determine block or allow
Choose policies that either block different groups from communicating or allow groups to communicate with specific groups. - Apply information barrier policies
These are activated and applied using cmdlets.
Sharing knowledge, while managing governance, compliance and enforcement risks
Here’s where you can define whether users can share sites and files externally from SharePoint. This will also define settings for OneDrive. Go to Microsoft 365 admin center > Settings > Org settings and then open SharePoint (external sharing):
Click one of the options for users to share with:
- Only people in your organization
- Existing guests only
- New & existing guests
- Anyone
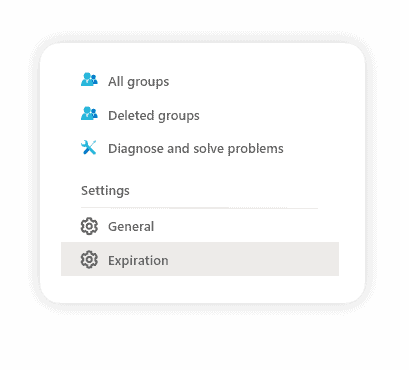
You can also set automatic expiry dates. These can be for external user access, or at a group level (requires Azure AD Premium subscription). Go to Azure Active Directory > Groups > Expiration to set the number of days:
Microsoft Viva: How to surface the right knowledge
Alongside the right configuration within Microsoft 365, good governance also relies on content staying up-to-date.
After all, employees will soon lose faith if they get recommendations and links to outdated knowledge sources. With so much information likely to be uploaded, it’s about controlling what can be indexed. Make sure employees avoid working on old or inactive content. To support Viva content and content creators, admins should ensure these three areas are covered:
- Policies
Build these into site designs and templates (making it easy for users to stay compliant) and automate with settings from the Admin Center. - Guidelines
Automate validation of content as much as possible, support users with education on how to define what is validated. - Roles and responsibilities
Content management to be incorporated into job descriptions and performance goals.
Choose how Viva Topics can find topics
This is available with the Microsoft 365 admin center > Viva Topics > Setup.
SharePoint integration means employees can access content remotely in the Viva Learning app. Naturally, this unlocks new ways to enhance knowledge and experiences. However, it also requires security and governance considerations.
SharePoint topic sources
You can select which SharePoint sites should be crawled for information:
- All sites
- All, except selected sites
- Only selected sites
- No sites
For example, you might want to hide sensitive topics for security, compliance, and privacy reasons.
Excluding topics
You can also upload a .csv with topics and match type (partial or exact). Choose to either:
- Don’t exclude any topics
- Exclude topics by name
Choose who can see topics
You can choose to make topics open to:
- Everyone in your organization
- Selected people or security groups
- No one
Choose who can create and edit topics
To help your governance, you can set topic management permissions. Choose who can create new topics or update existing topic details, such as description, documents, and connected people:
- Everyone in your organization
- Selected people or security groups
- No one
Choose who can manage topics (knowledge managers)
You can limit who has access to the topic management dashboard. Assign knowledge managers who can:
- Confirm
- Reject
- View topic feedback
- View, create, and edit topics
After you’ve set all the necessary permissions, it’s time to create the topic center in SharePoint. Enter the site name and a description including the topics and click Activate.
Enable Microsoft Viva governance with Syskit Point
Minimizing clutter is at the heart of success with Microsoft Viva. That’s why it’s essential to identify inactive resources, users, and content. With options to automate governance – while also maintaining a full overview of your Microsoft 365 environment. This benefits both IT administrators as well as business owners, giving peace-of-mind that content is only being shared among the right groups.
You gain all this with Syskit Point.
Detect inactive guest users
Make sure you always have the right number of guests in your environment. Syskit tracks activity and alerts you within a single-pane dashboard. You can choose the resulting action, from deactivating accounts to sending notifications to managers:
Identify inactive content
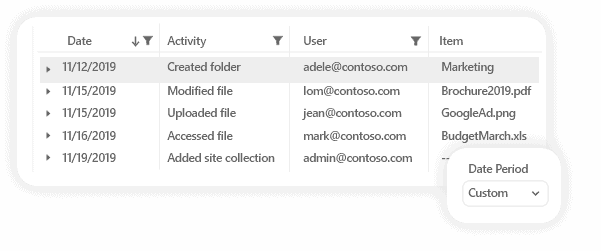
Keep Microsoft Viva and your Microsoft 365 tenant clutter-free, surfacing only the relevant content. You define what counts as inactive content, for example, the number of days without any activity. It’s all done for you using Microsoft 365 audit logs and usage reports across SharePoint, Exchange, Yammer, and Teams:
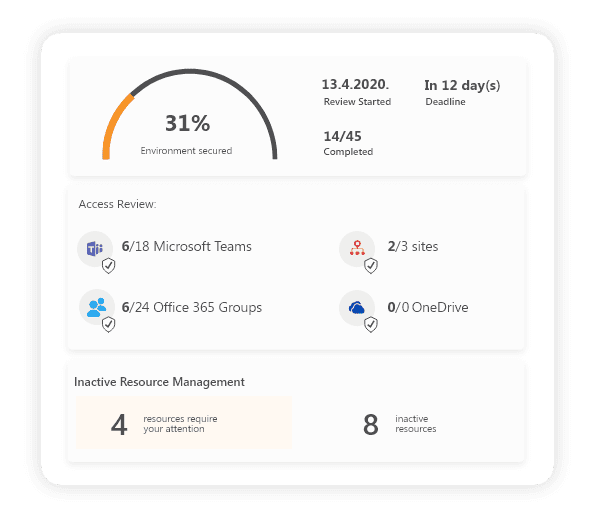
Schedule access reviews and lifecycle management
Admins can specify tasks to govern, and how often. They see the progress and can send automated reminders to owners, asking them to complete their designated actions. Sensitive content can be managed, have multiple policies applied, and have advanced access reviews to cover:
- Whether internal and external users have access to the right resources, with the right permissions or group memberships
- Audit log checks for unwanted permission changes
- Sharing options for external-facing content
- Corrections made to any discovered errors
Limit workspace creation (with templates)
While Admins can limit group creation in Microsoft Viva, Syskit Point takes things further. You get three pre-configured templates to help define and control workspace creation. These are for managing a project, department team, and public team.
You can apply these across Teams, SharePoint, Yammer, and M365 Groups. This also includes the ability to create naming rules, just like you would in Microsoft 365. However, with Syskit templates, you won’t have to start from scratch.
Start a free trial of Syskit Point today and discover how to automate and optimize Microsoft Viva governance.