Using Azure Conditional Access when security defaults isn’t enough
Table of contents
Security Defaults and Conditional Access are steps along the journey to Zero Trust security. Zero Trust is a whitelisted network strategy that reduces the potential attack surface of your organization. It does this by excluding all unauthorized entities, such as users, devices, and applications.
A Q&A discussion at Microsoft Ignite 2021 with Stefan van der Wiele, Senior Program Manager at Microsoft, and Peter van Leeuwen, Senior Program Manager at Microsoft inspired this post.
What is Azure Security Defaults?
Security Defaults is the preconfigured settings in Microsoft Azure. It is available at any Azure license level and turned on by default for all new tenants.
Security Defaults features the following:
- Multi-factor authentication (MFA): multi-factor authentication is a type of authentication that requires the use of two or more verification factors to gain access to a system. Azure MFA offers a 14 day grace period after being initiated. This period allows users to register before it becomes a requirement after 14 days.
- Administrator protection: the Azure AD administrator role members will have to perform additional authentication to log in. In short, if you’re an admin, you will always need to use MFA.
- Improved protection for all users: Users will be required to use additional authentication when certain events occur, like when they authenticate using a new device, use a new application, or perform critical tasks.
- Blocking authentication of legacy applications: Since legacy applications do not support multi-factor authentication, they are blocked when Security Defaults is enabled.
Security Defaults can be a great place to start. It’s a great place to start for organizations that aren’t sure how or where to improve their security posture. For organizations that use the free tier of Azure active directory license, Security Defaults will be the only option.
You will need to find the balance between security and end-user productivity. If the defaults are enough, then it’s great to go with Security Defaults, but most enterprises need more control using Conditional Access.
What is Azure Conditional Access?
In organizations that need to use security signals and make decisions to enforce policies, Conditional Access is the way to go. In cases where an organization has complex security requirements, it’s an excellent time to consider Conditional Access.
Conditional Access ensures that your users can only perform specific actions when they meet certain criteria. For example, you could limit viewing sales data to reps that have been in the company for two years. Or control who can download an app – maybe only devs with API access or developers who have passed a certification exam.
To use Conditional Access, an Azure admin must disable Security Defaults.
Conditional Access has several benefits, including:
- Improving productivity by only having a user sign in using MFA when specific signals warrant it
- Reducing risk by detecting unusual activity patterns and sending alerts when they occur
- Improving compliance by auditing access to applications and presenting terms of use for user consent upon entry
- Reducing cost by reducing the reliance on third-party customer solutions for security
- Moving closer to a zero-trust environment
Using Conditional Access policies allows admins to make decisions and then enforce organizational policies. You can think of Conditional Access as an if-then statement for access and assignments. If a condition is met, then apply these access settings. However, You will need an Azure AD Premium P1 or P2 license for this kind of setup.
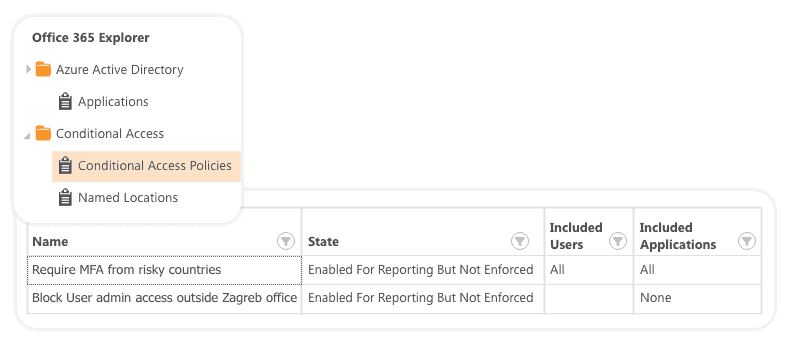
If you want to track all your Azure AD Conditional Access settings along with other AAD settings, you don’t have to go back and forth through your admin interface. Syskit Point is a central reporting solution that will give you a single pane view for all settings in your AAD and Office 365.
Making sure everything is protected
The good news is everyone is protected with Security Defaults by default. This protection is part of the free and lower-paid licensing packages. For those organizations that use the premium edition of Azure active directory, Conditional Access may be a good option when they want to fine-tune their security settings, improve signals and decision-making, and better enforce organizational policies.

