Office 365 Security Hacks for Admins
Table of contents
Have Control Over SharePoint Permissions
As an Office 365 admin, a part of your job is to report to your superiors and answer questions such as:
- Who can see the content of my site collections?
- Who can access Office 365 groups and to what level?
To get the answers, you must go to each group to see which members have access to which content. You can use the Check permissions option in SharePoint UI, but you can only search permissions for one user at a time. Imagine the amount of time that an admin who is working in a big corporation would have spent on checking permissions for every single user.
With Syskit Point, you have a complete overview of who has access to what and, thus, complete control of all permissions. You will find all the members and their permissions for every selected object with a Permissions Matrix. Or, you can use the Permissions Level Usage Report to find out which permission levels have been granted across site collections.
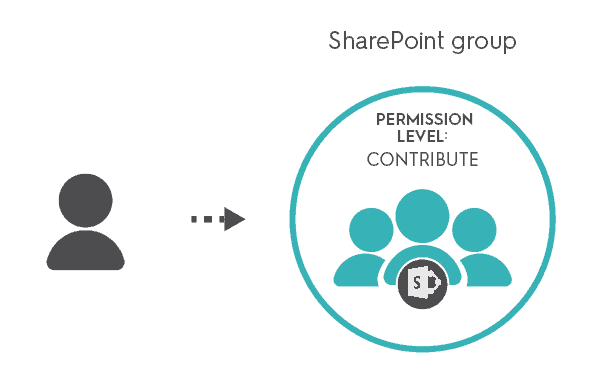
Add user permissions through SharePoint groups
You already know that giving permissions directlyon adocument and/or list item is not such a wise idea. If you follow that practice for a long time, you will soon lose track of all the direct permissions that your users have. This is especially tricky in situations when a permission structure changes, like when users leave a company or change departments.
If you want to avoid confusion and save time, the best practice is to add users to SharePoint groups and apply permissions to these groups. This way, you’ll be sure that permissions are well organized and easy to manage.
With Syskit Point’s Directly Assigned Permissions Report, you will avoid having too many direct permissions in your tenant and will stay compliant with Microsoft recommendations.
Keep the number of unique permissions at a minimum
As you know, SharePoint sites inherit permissions from their “parent”. Permission inheritance enables you to assign a permission once and have it apply to all “child” sites, lists, libraries, folders, and items. That saves time and makes the administration of permissions a whole lot easier.
However, some situations require you to break the inheritance and create unique permissions. That’s where things get complicated. Even a simple task of granting permissions becomes an impossible mission when permission inheritance is broken. On top of that, unique permissions are hard to keep track of and they can decrease the performance of your tenant.
If you have to break permissions inheritance, you should avoid breaking it at lower levels of content hierarchy. For example, you can make a separate SharePoint group with a desired permission level and, then, make a user a member of that group.
Syskit Point has a solution for you. With a Unique Permissions Report, you can find all the objects with unique permissions in your tenant.
Find more pro tips for Office 365 security in our free eBook
Office 365 Security Hacks for Admins


