4 steps to minimize oversharing and stay Copilot ready
Table of contents
Oversharing – content shared beyond the necessary audience – is a major stumbling block for organizations looking to expand their use of Copilot. Avivah Litan, VP and Distinguished Analyst at Gartner, recently publicly shared that their latest research has shown that nearly 30% of enterprises experienced a breach against their AI systems, and 62% had data compromised by an internal party. In other words, data compromise due to oversharing.
This is where Syskit Point steps in. Long before “oversharing” became a buzzword, Syskit Point was on the front lines, addressing who has access to what and minimizing unnecessary sharing and permissions. Essentially, Syskit Point has always been about making your environment “Copilot Ready” by enabling effective management of who has access to what, quickly addressing and removing unnecessary permissions.
More importantly, Syskit Point helps you stay “Copilot Ready” in the long term. How? By empowering workspace owners to keep their workspaces clean of unnecessary sharing and permissions through delegated management.
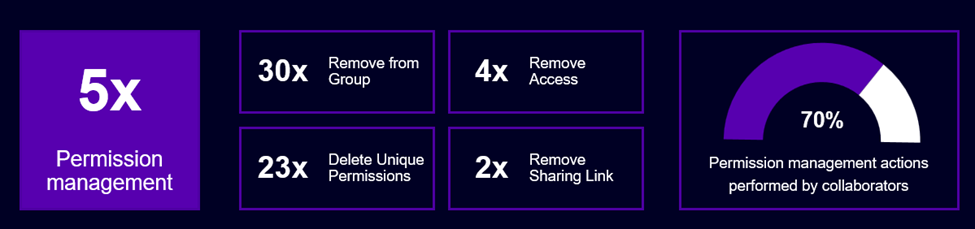
We’ve seen that organizations that delegate workspace management to end users manage permissions on average five times more than the ones that don’t. On a closer look, 70% of those actions were done by workspace owners, making delegated management pivotal in their fight against oversharing.
In this blog, we’ll walk you through the 4P process:
- Prepare,
- Purge,
- Prevent,
- Protect.
We often implement the 4P process to help organizations tackle oversharing challenges effectively. Let’s dive into how this approach can secure your data and optimize your digital M365 workspace.
Prepare & Purge: You can’t manage what you can’t see
The Prepare phase is your first line of defense against oversharing. It involves establishing an understanding of the current data sharing and access landscape across your organization. With Syskit Point, you gain the necessary tools to assess and gain visibility into every facet of your current sharing and permissions. However, quickly mitigating your oversharing is critical in this phase. That’s why, in all our reports, you can immediately perform management actions; even more importantly, you can perform those actions in bulk.
Key features of the Prepare & Purge phase
Group Access Report
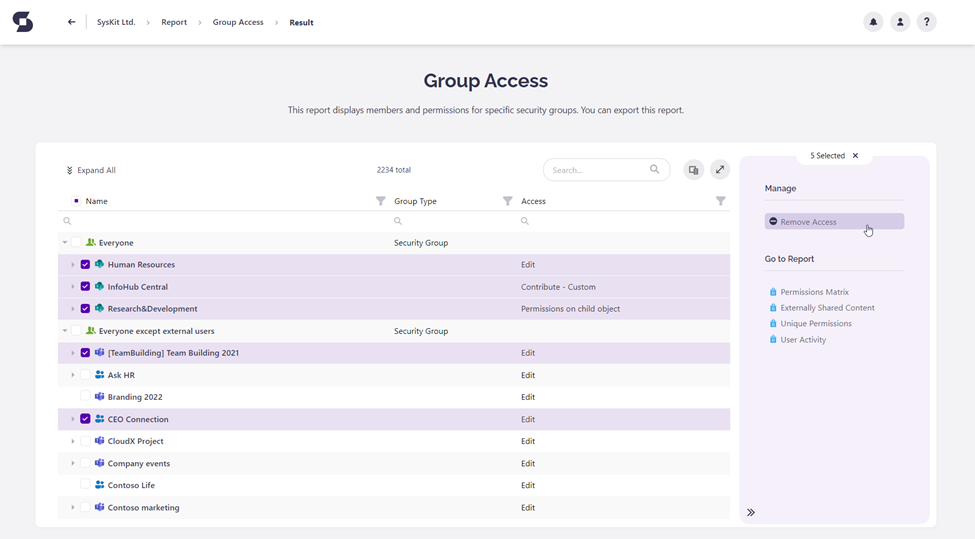
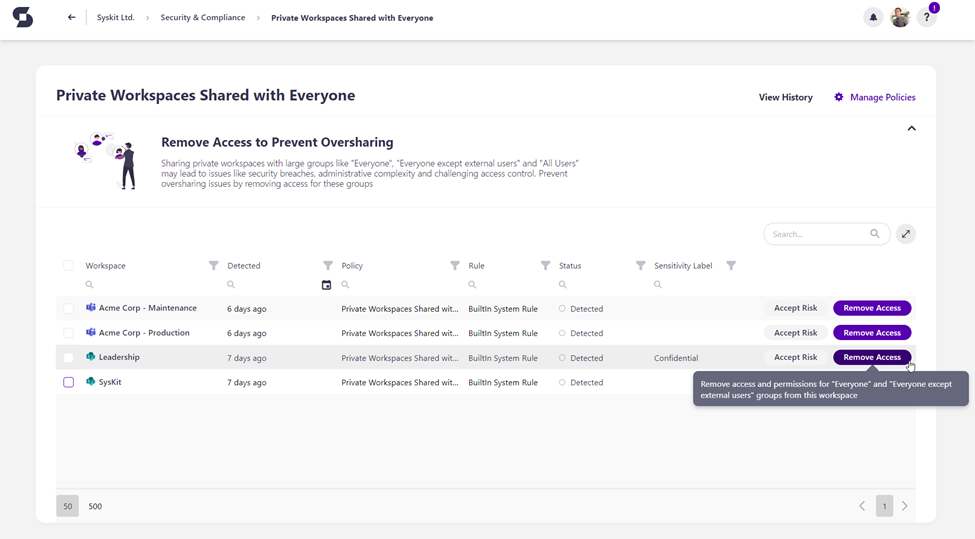
One of the most common challenges is oversharing through large groups, most notably the “Everyone Except External Users” group, which will effectively allow access to all users in the organization except external users.
Using our Group Access report, you can evaluate where Everyone Except External Users, as well as any other large M365 Group, Microsoft Team, or Security group, have access to and remove this access in bulk straight from the report, immediately minimizing oversharing.
Sharing Links Report
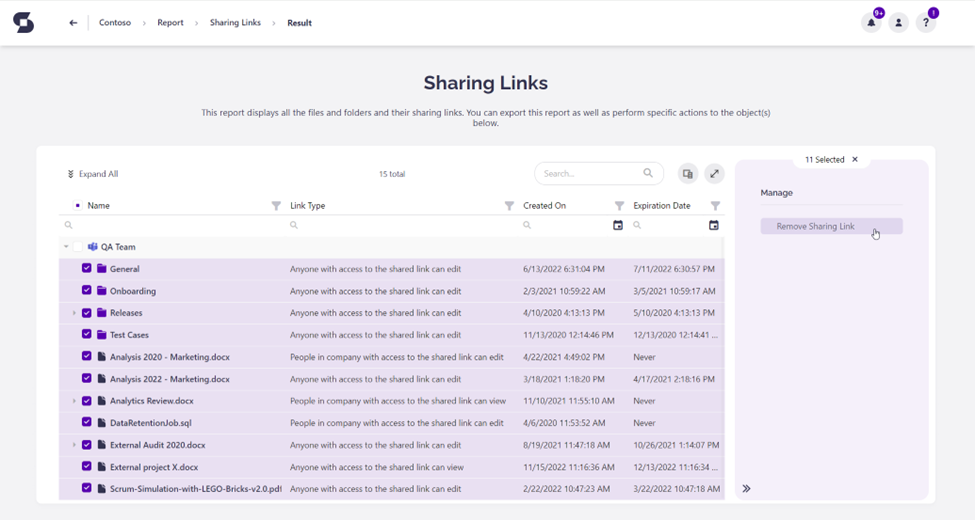
The other significant risk in any environment is the improper use of sharing links, especially anonymous ones, and company-wide sharing links, which can lead to uncontrolled data leaks if not managed correctly.
Syskit Point tackles this challenge head-on with our Sharing Links report, where you can quickly assess all sharing links, including company-wide and anonymous links, and remove them in bulk from within the report – ensuring that information remains secure and accessible only to intended recipients.
Public Workspaces
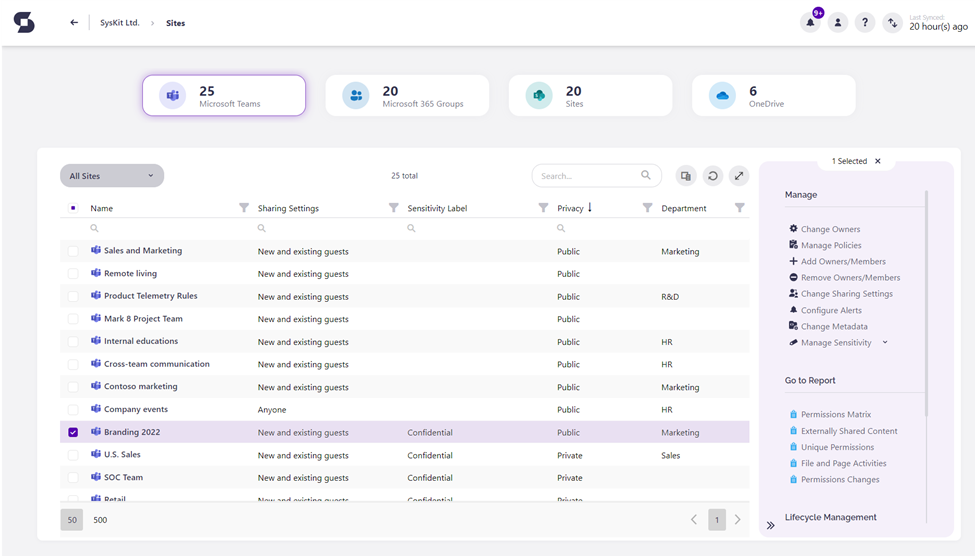
Microsoft Teams that were mistakenly set to public can pose a significant oversharing risk. Sometimes, these settings might be appropriate but can lead to unintended data exposure if not regularly reviewed and correctly configured.
Through the Sites Overview report, IT Teams can get an overview of all public workspaces and discuss with owners whether they should be public, ensuring that workspaces are public if necessary.
Prevent & Protect: Ensure oversharing is continuously addressed
After addressing the immediate concerns of oversharing through the Prepare and Purge phases, organizations must ensure that such issues do not recur. This is where the Prevent and Protect phases come into play. Organizations can easily implement strategies to maintain ongoing vigilance and control over data-sharing practices with Syskit Point.
Let’s dive into these strategies and how they help organizations keep their Microsoft 365 environments oversharing-free.
Strategies and key features of the Prepare & Purge phase
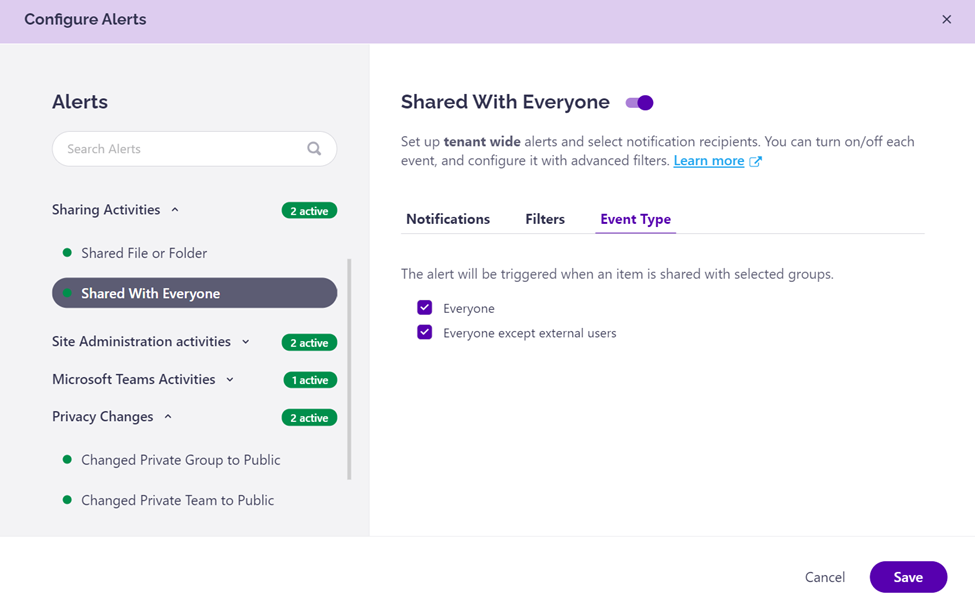
Real-time alerts for sharing activities and privacy changes
Setting up Syskit Point to send immediate alerts for sharing activities with everyone groups or changes in privacy settings is extremely useful. This enables IT teams and/or workspace owners to act swiftly and rectify any potentially risky sharing before it becomes problematic. Learn how to set up alerts here.
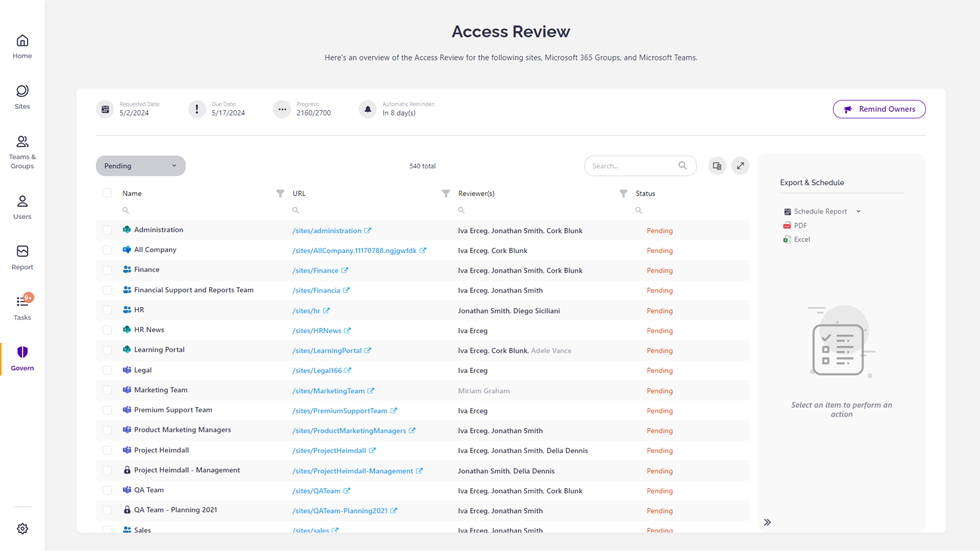
Governance automation rules and Access Reviews
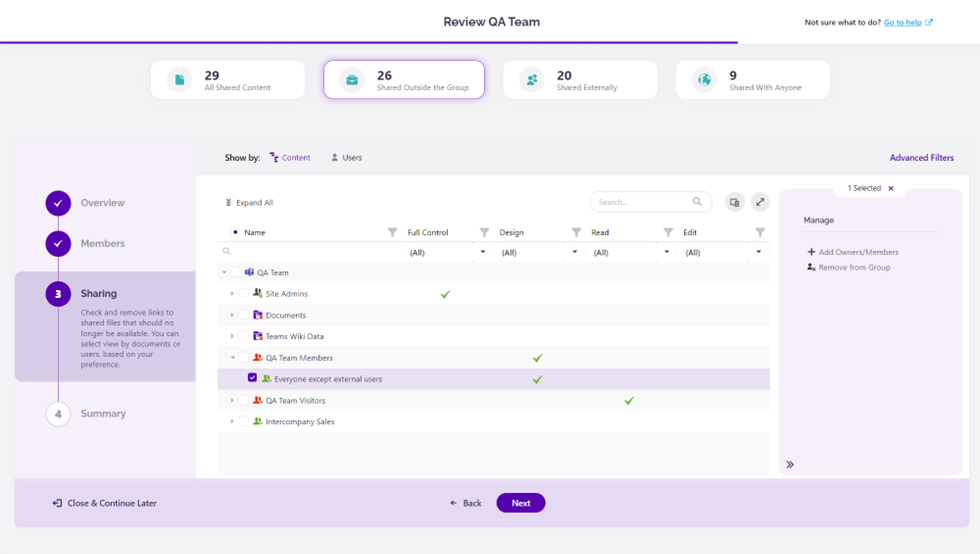
Remember those stats from the beginning? Organizations that delegate workspace management to end users manage permissions on average five times more than those that don’t—well, this is their secret sauce! Run Access Reviews to ensure that workspace owners address oversharing regularly.
With Access Review policies, IT teams delegate permissions management to the workspace owners who are more familiar with who should have access to the content in their workspaces. This ensures that permissions and membership are continuously reviewed, resulting in significantly less oversharing.
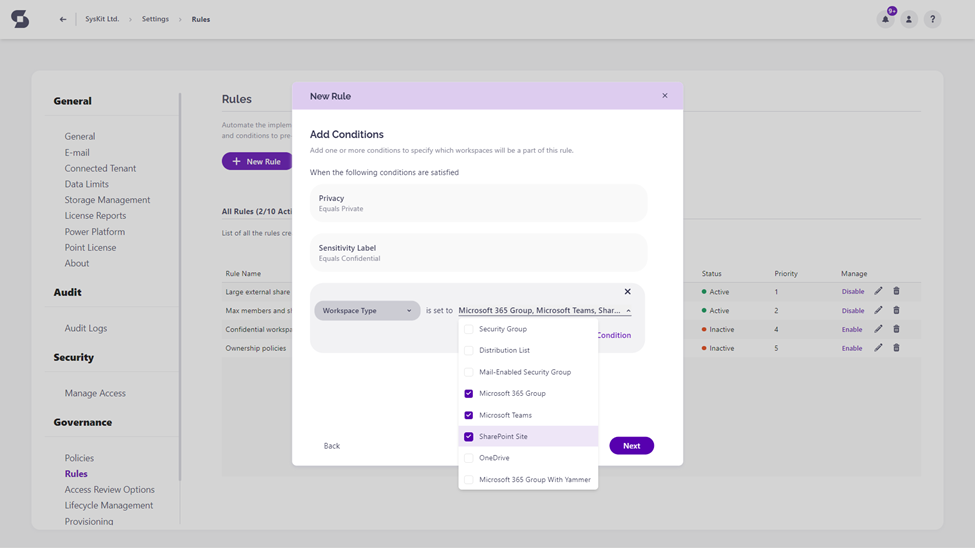
On the flip side, we know that applying policies is a cumbersome task, and often, there are some unintentional oversights. Even if you’ve done everything correctly, things will change, meaning that you’ll need to constantly update which policies are applied to your workspaces.
Well, that is where Governance Automation Rules come in place. You can think of our Governance Automation rules as your virtual assistant who monitors your environment daily to ensure that the proper Access Reviews are applied to workspaces based on the rules you’ve set up, regardless of how and when those workspaces were created.
After creating or updating the workspace, Syskit Point assigns all the necessary policies, including the Access Reviews. AUTOMATICALLY! This ensures that all workspaces are reviewed regularly, maintaining them as oversharing-free.
Inactive workspace detection and disposal
Obviously, the fewer unnecessary workspaces you have, the lower the risk of oversharing. Inactive workspaces can be a source of oversharing vulnerabilities but also a source of information for Copilot to confidently provide wrong answers with outdated information to your end users. So, automating the detection and disposal of inactive workspaces has more than one benefit, including minimizing the footprint for potential oversharing.
Stay in control
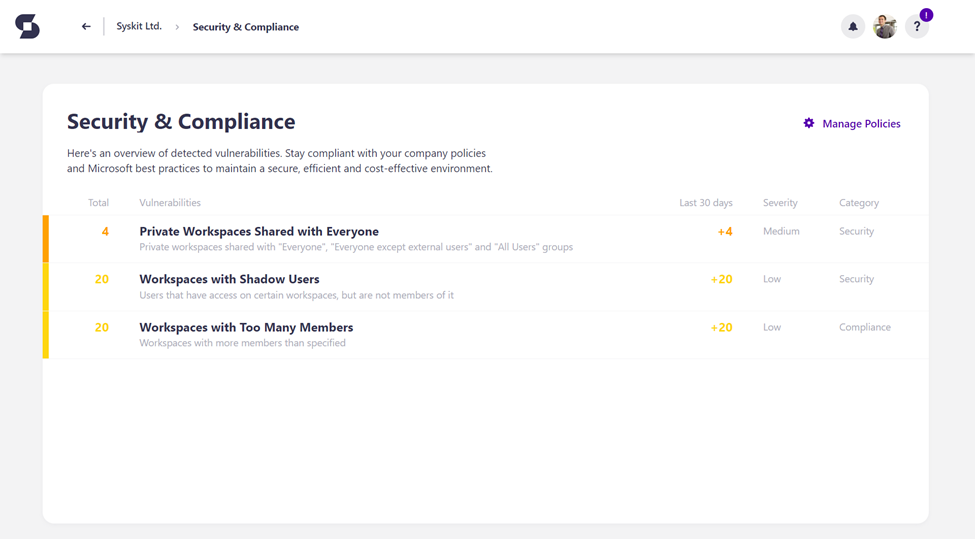
And the cherry on the top is that IT teams always stay in control. With Syskit Point’s governance dashboard and Security & Compliance dashboard, IT teams can monitor the ongoing progress and quickly address any oversharing vulnerabilities as they arise.
At any time, you can see how your scheduled Access Reviews are progressing and what actions the owners performed. You can also remind the owners who might have “forgotten” to review their workspaces.
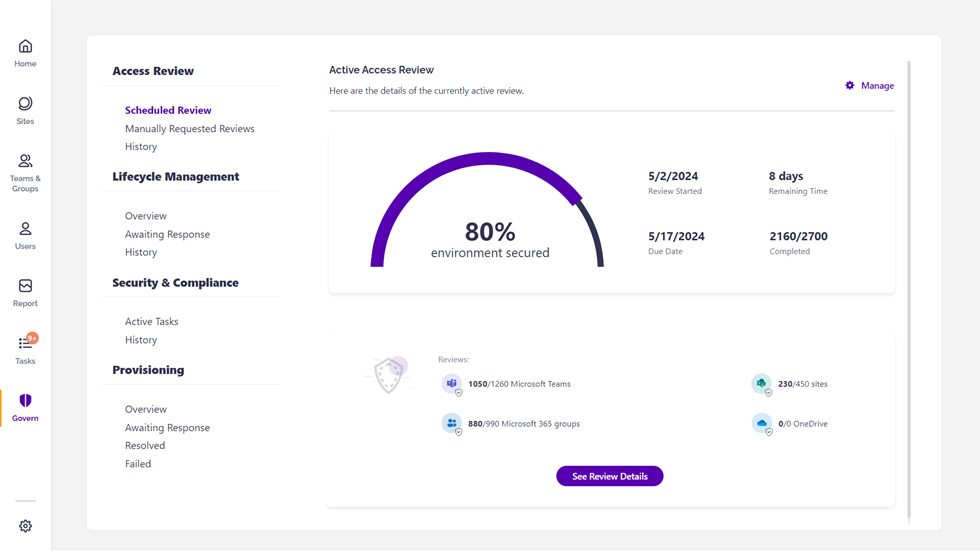
In addition, you can also stay on top of the essential oversharing vulnerabilities through our Security & Compliance Dashboard by monitoring which private workspaces are shared with everyone, which workspaces have non-members access to the content, and which workspaces have a suspiciously high number of members—we often see customers having challenges with nested groups.
Last thoughts on oversharing and Copilot
By adopting the 4P strategy, you can ensure your organization’s Microsoft 365 environment is secure, oversharing free, and truly “Copilot Ready” – in the long run! Ready to see how Syskit Point can help you minimize oversharing and boost your security? Get in touch with us today.


