Server performance, user activity, and application usage
Trusted by
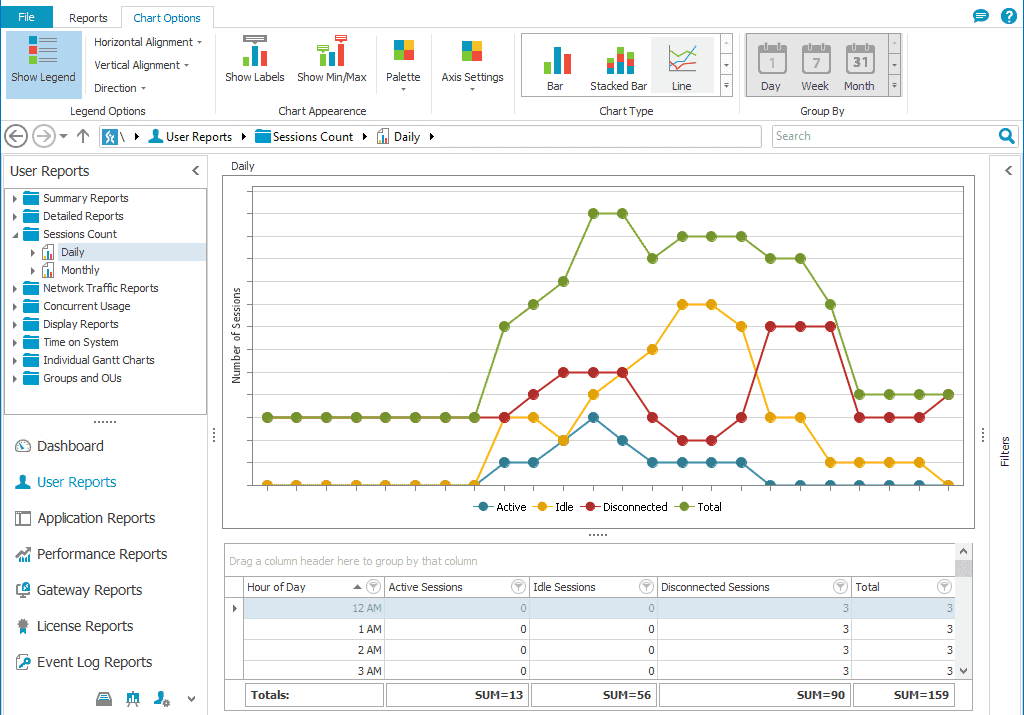
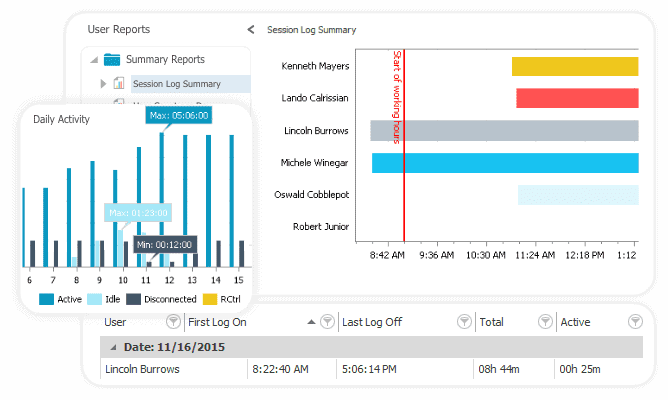
Monitor user activity
Keep track of RDP connections accompanied by useful remote user session reports. Stay on top of user logons, logoffs, and remote connections to servers to see who’s doing what, where, and when.
Audit user activity to determine the number of users in a given timeline and detect your most active or idle users.
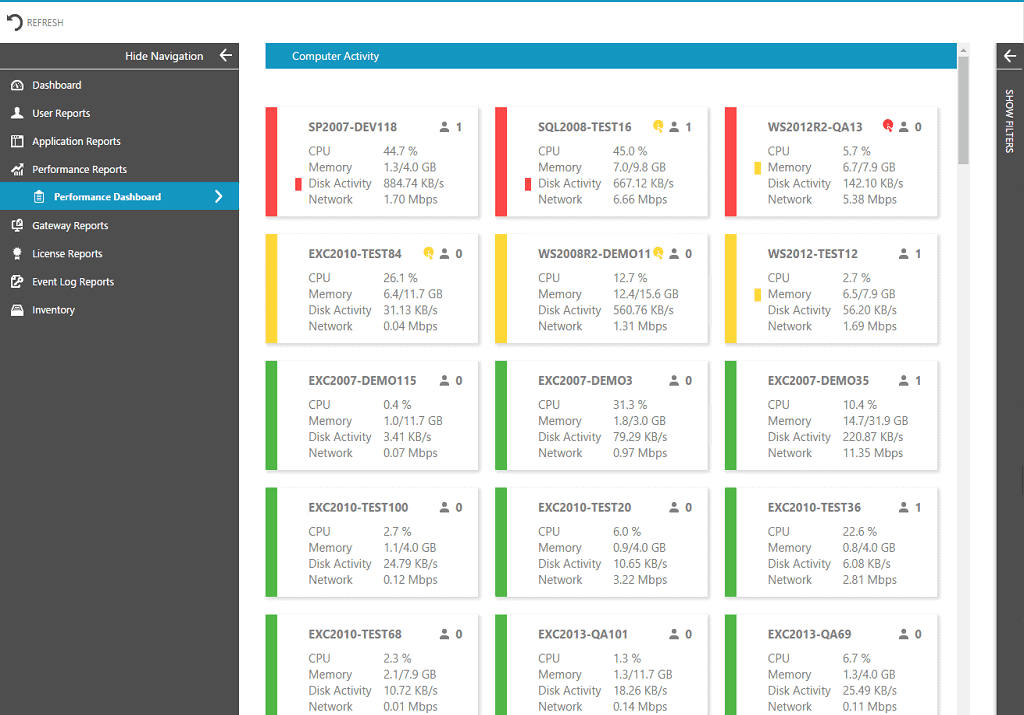
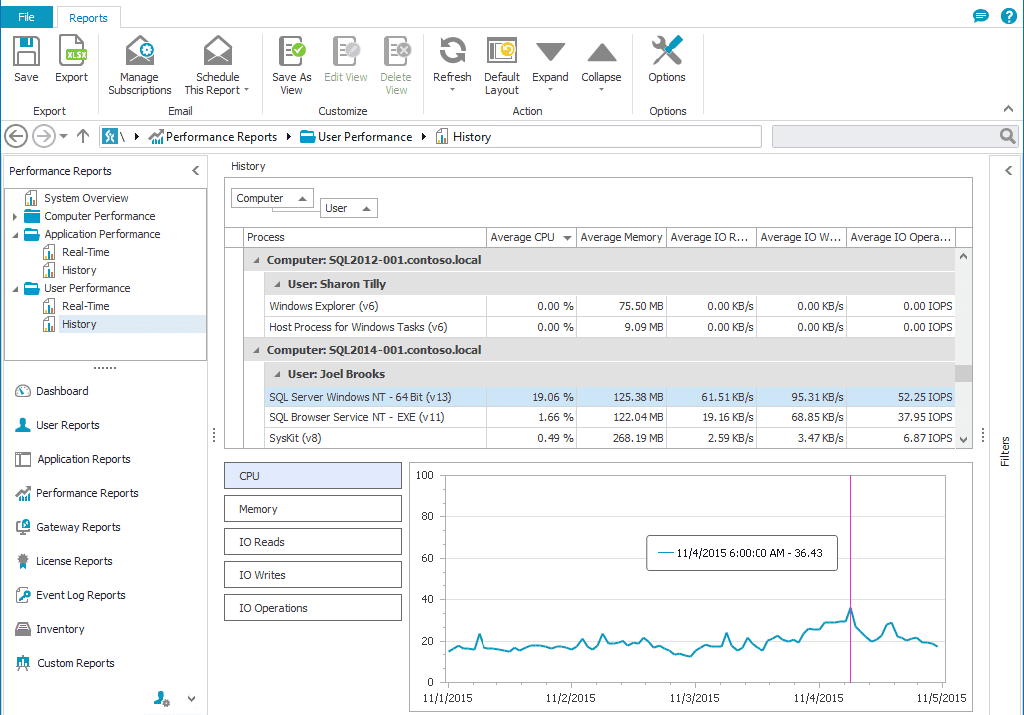
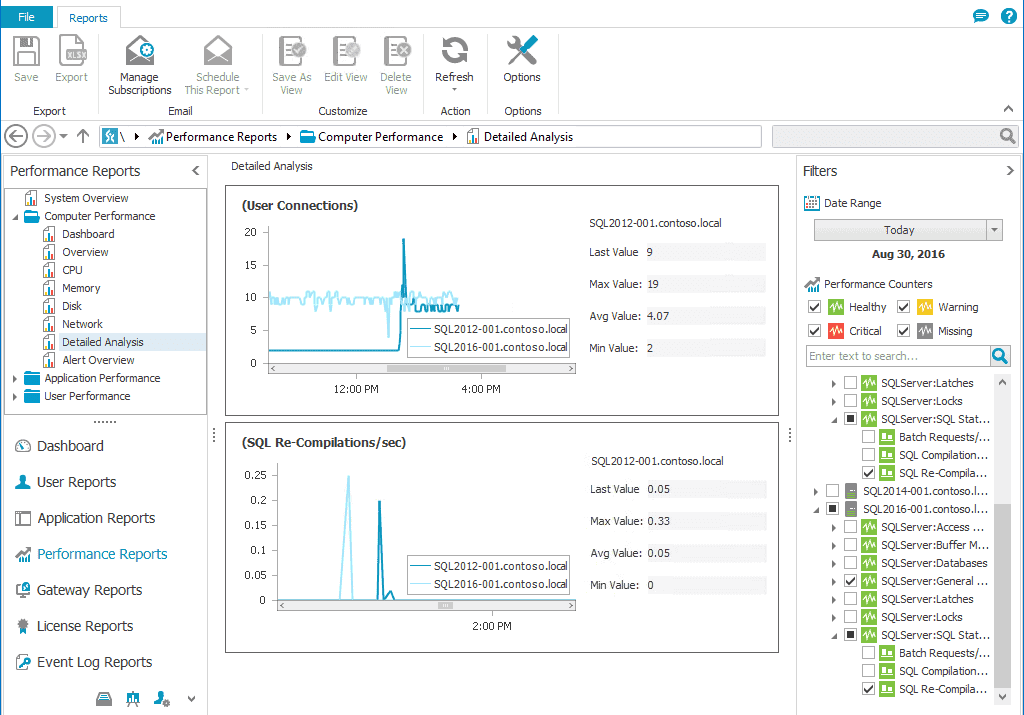
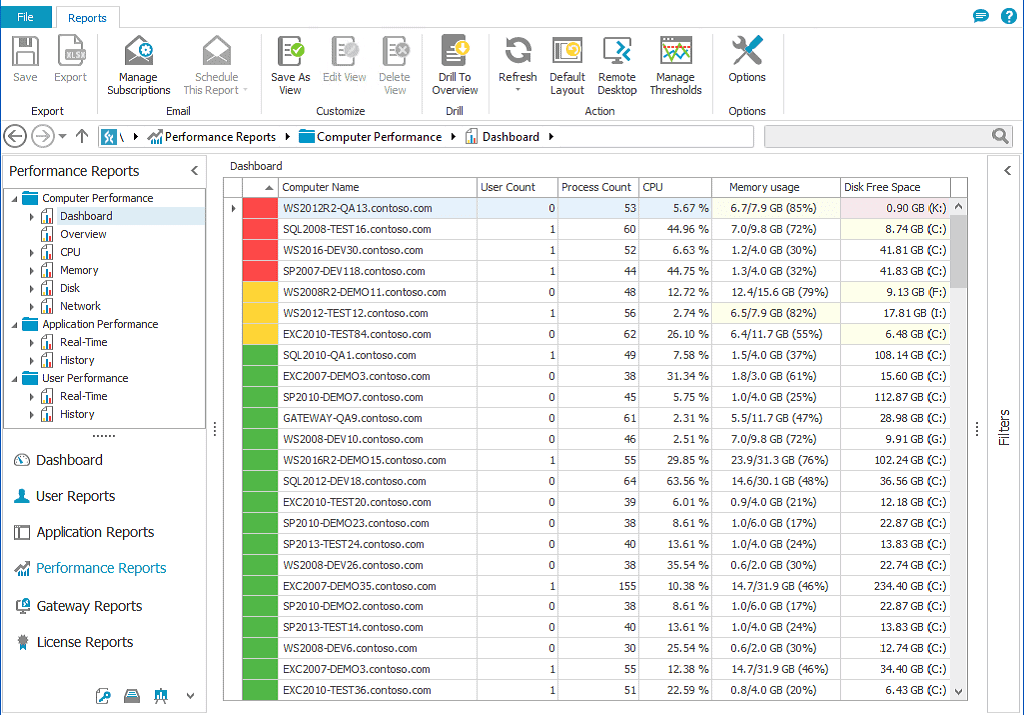
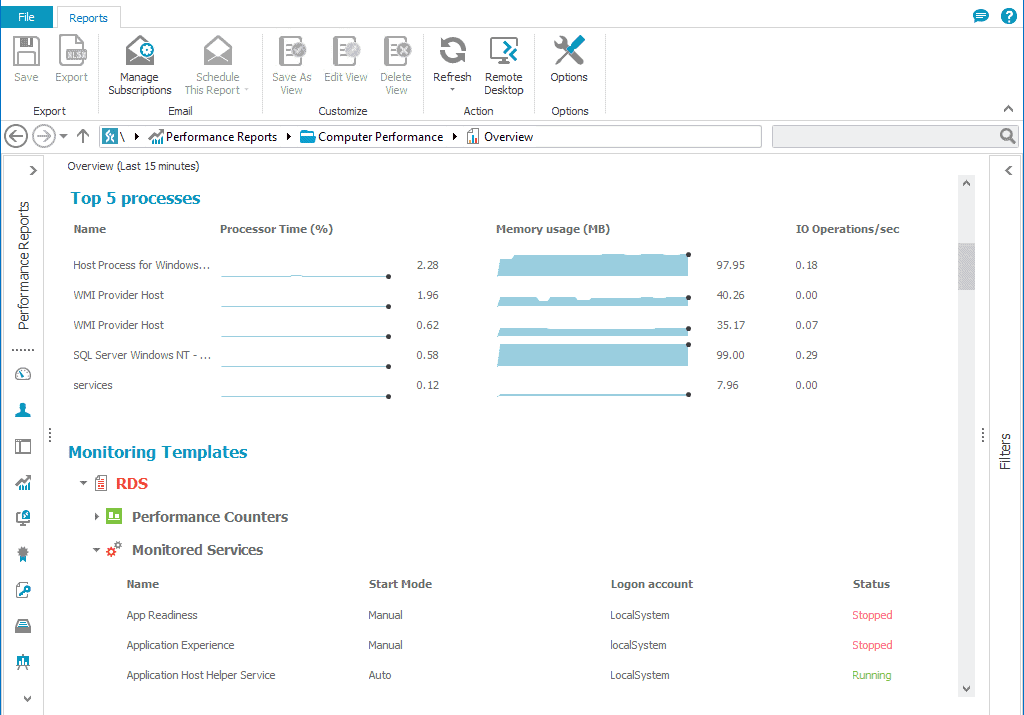
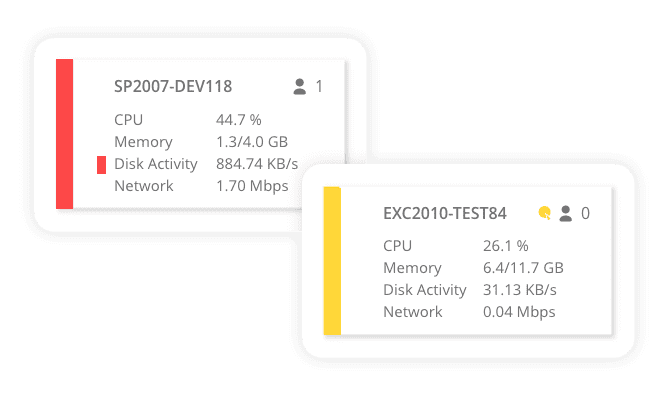
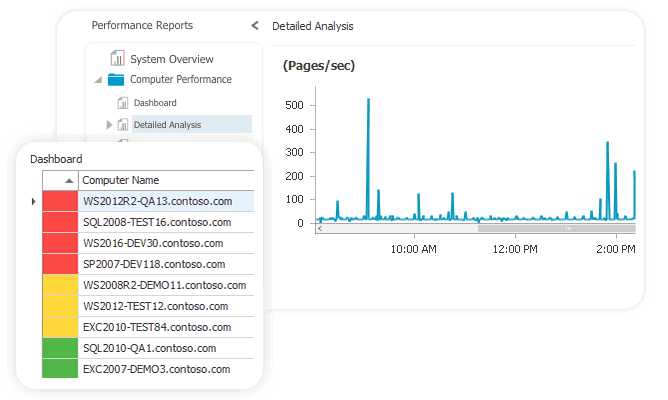
Server performance monitoring
Real-time server performance reports enable you to monitor all important metrics, including CPU, memory, and disk usage, as well as specific metrics, such as SQL transactions, current IIS connections, or current IIS anonymous users.
Stop performance issues before they cause sluggish server response times or even service crashes.
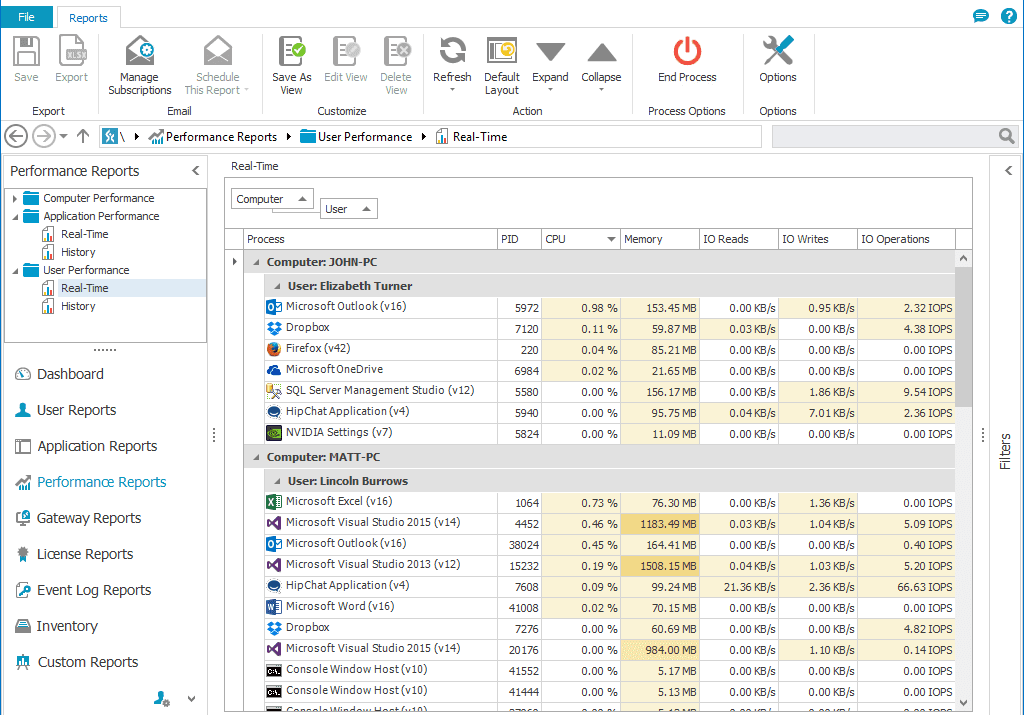
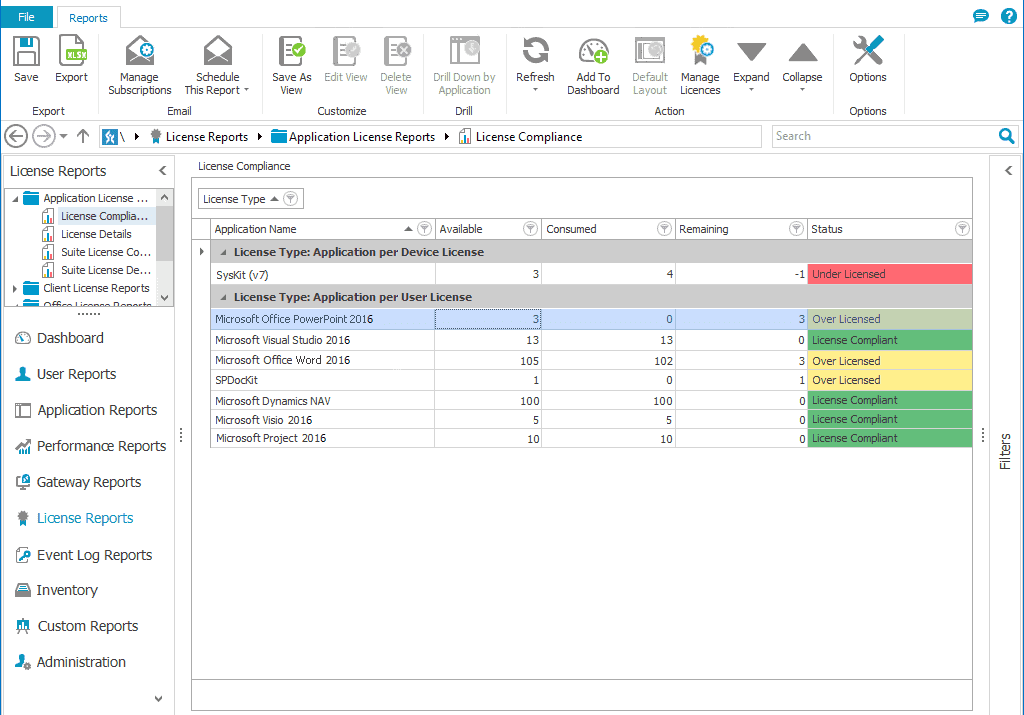
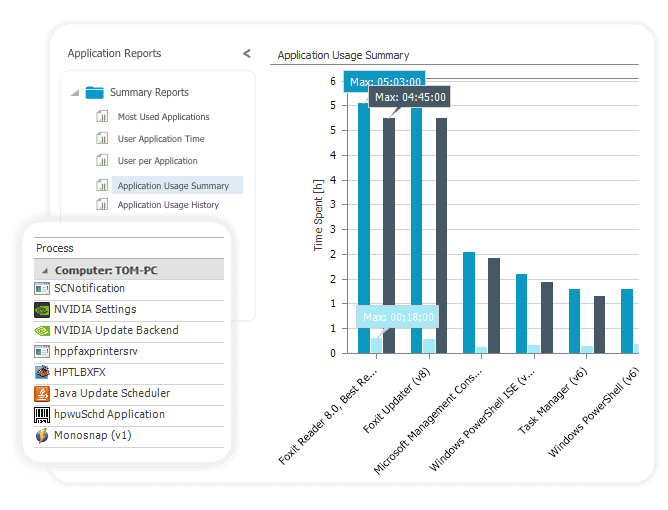
Application usage monitoring
Track application usage on your servers to find out which users were using certain applications and for how long. Determine the most used applications, the number of application instances, and concurrent application usage.
Find out if employees are using published applications effectively and during their working hours.
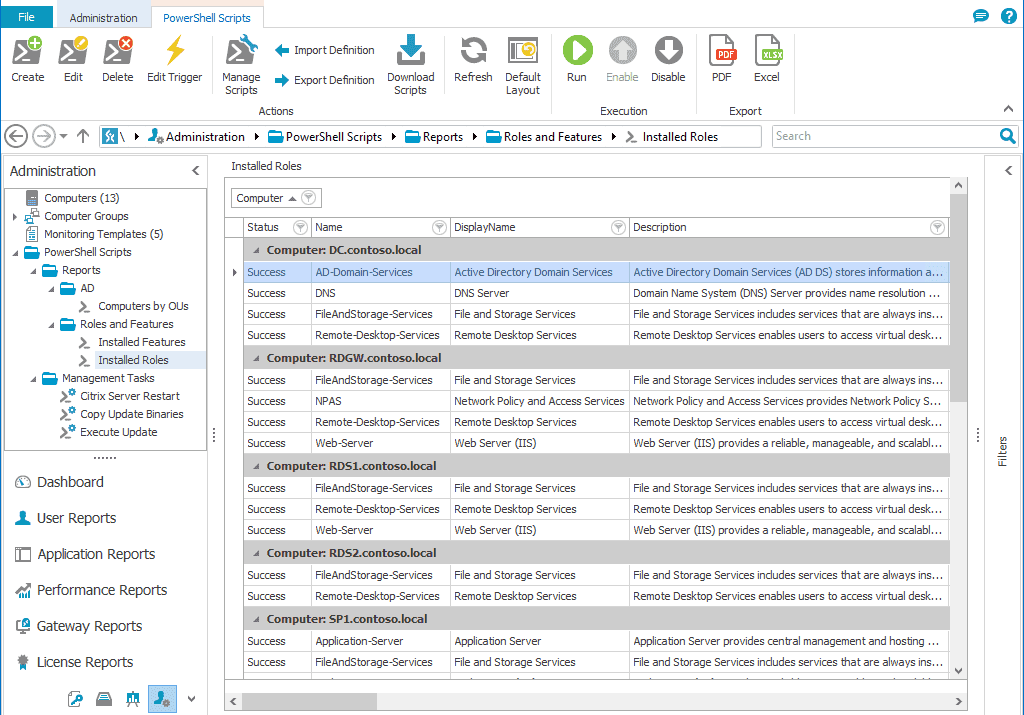
One tool to monitor them all
We have designed Syskit Monitor to be a single application for all your servers and platforms monitoring, including:
- Citrix Virtual Apps and Desktops monitoring
- SharePoint, SQL, and Windows Server monitoring
- Remote Desktop Services and Gateway monitoring
It comes with a quick installation containing built-in prerequisites and is available as a desktop and web interface.