Windows file auditing – How to secure files on your servers
Table of contents
Gaining insight into what’s going on in your server environment is crucial, especially when it comes to object-access auditing and finer details like Windows file auditing.
Auditing object access means determining who accessed what and when on your file system, and you can audit all objects, not just files and folders but registry keys, printers, and services.
What most sysadmins want to know is who accessed which file and edited, modified, renamed, or even deleted a certain file or folder. If sensitive data has been compromised in any way, time is of the essence. The longer the incident goes undetected, the more damage it can cause.
For instance, how would you know who tried to access a file they have no business opening? Especially when multiple users have access to certain confidential data such as financial records, medical records, accounts, and employee folders.
These auditing policies should be updated regularly, not just for the sake of satisfying basic data security regulations. With new technologies and growing IT systems, it’s becoming more and more difficult to manage user permissions and privileged access.
Windows file auditing: How to properly secure files on your servers
Security on Windows servers goes through the NT File System, which includes the SACL, or Security Access Control List, a mechanism for tracking object access on the servers.
File and folder auditing can be managed in two ways: using the Group Policy or locally with the Security Policy for individual servers.
You will find the Audit File System options under Local Security Policy > System Audit Policies > Object Access.
When you have just one or two servers and need to keep track of only a couple of local files and folders, you can set the whole thing locally.
However, if you have more servers, it’s recommended that you configure the Windows file auditing policy via Active Directory, and the policy will be applied to all of your servers and workstations. Additionally, this is the best way to track and audit more objects automatically without the hassle of manually clicking each setting.
Windows file auditing best practices:
- Don’t add individual user accounts directly to the Access Control List.
- Create multiple groups, and add them to the ACL.
- When you have just one user who will be accessing a certain file, place the user in a separate group, and add the group to the ACL.
Track successful and failed file accessing
The first thing you need to do is enable file access auditing on your server.
By default, Audit Object Access isn’t turned on—you must configure it manually. But before that, you need to configure the local group policy or Group Policy Object (GPO) in the Active Directory. After you’ve done that, you can go to the Audit Object Access properties and decide whether you want to turn on tracking options for successful or failed access, or both.
The third thing you must do is choose which actions you want to be audited, which types of accesses, and why, directly at the data level The “why” comes because there’s no point in auditing every single action someone made on a workstation or server. I mean, you can configure your auditing policy as such, but you will slow down your server, cram up your log events and cause mayhem with the volume of indexing.
How to configure Group Policy and file auditing on Windows servers
Here’s a step-by-step guide on how to enable Windows file auditing.
You must log in to the Domain Controller to check whether you have Group Policy Management enabled.
In the Enable Folder Auditing article, you will find 1) how to configure Group Policy for a domain without the Group Policy Management feature, as well as 2) how to configure it with the Group Policy Management feature and how to configure Windows file auditing.
Problem: Viewing file audit results
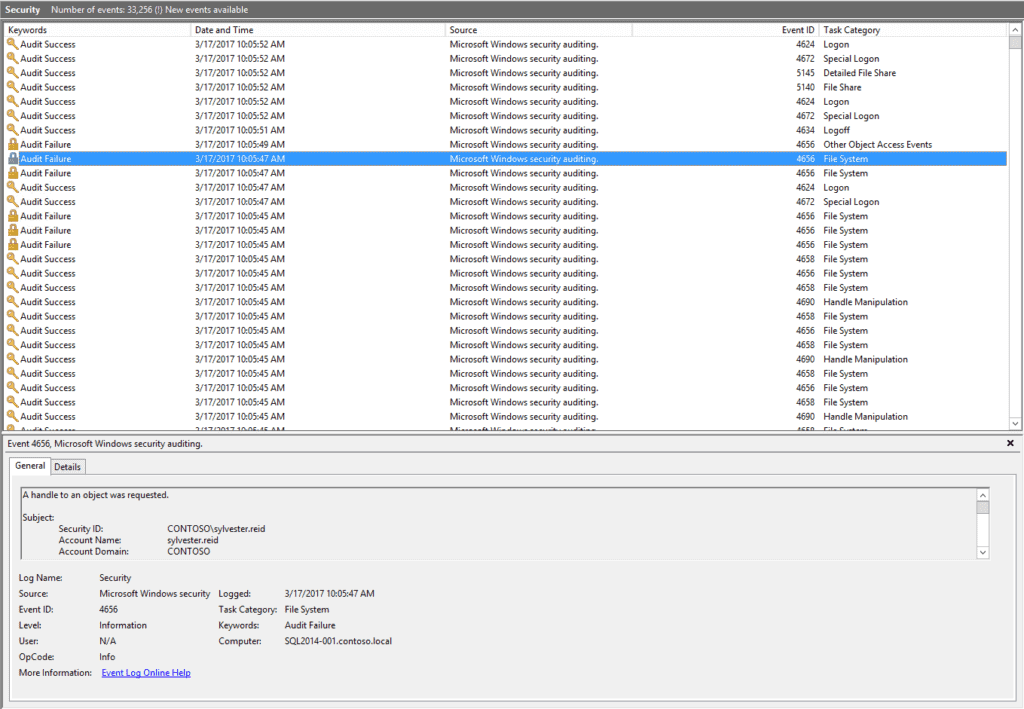
If you don’t have a third-party Windows file auditing solution, you will have to get accustomed to using the Windows Security Event Log to manually review who did what, when, and where. That’s just the tip of the iceberg.
Managing security event logs is a painstaking job, especially if you’re in charge of a collaborative work environment. The one problem is that Windows file auditing can log only an occurrence of a certain file change, but it cannot provide details about before and after states.
Solution: Syskit Monitor
Track all security-related events in your environment from a single console by using Syskit Monitor.
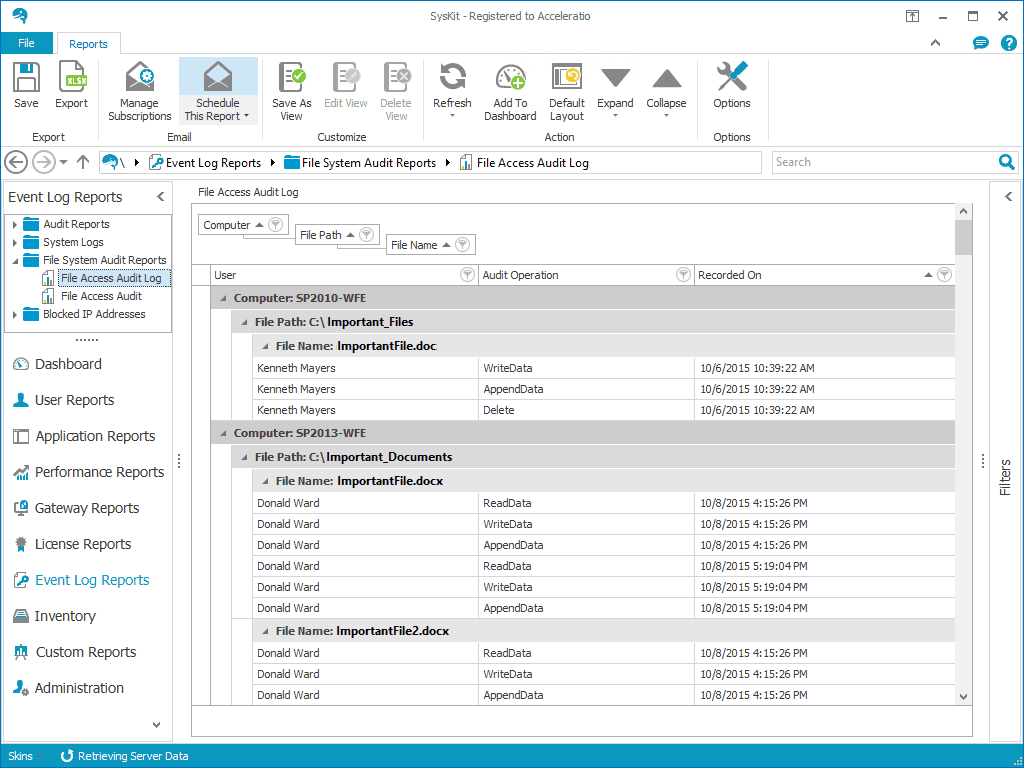
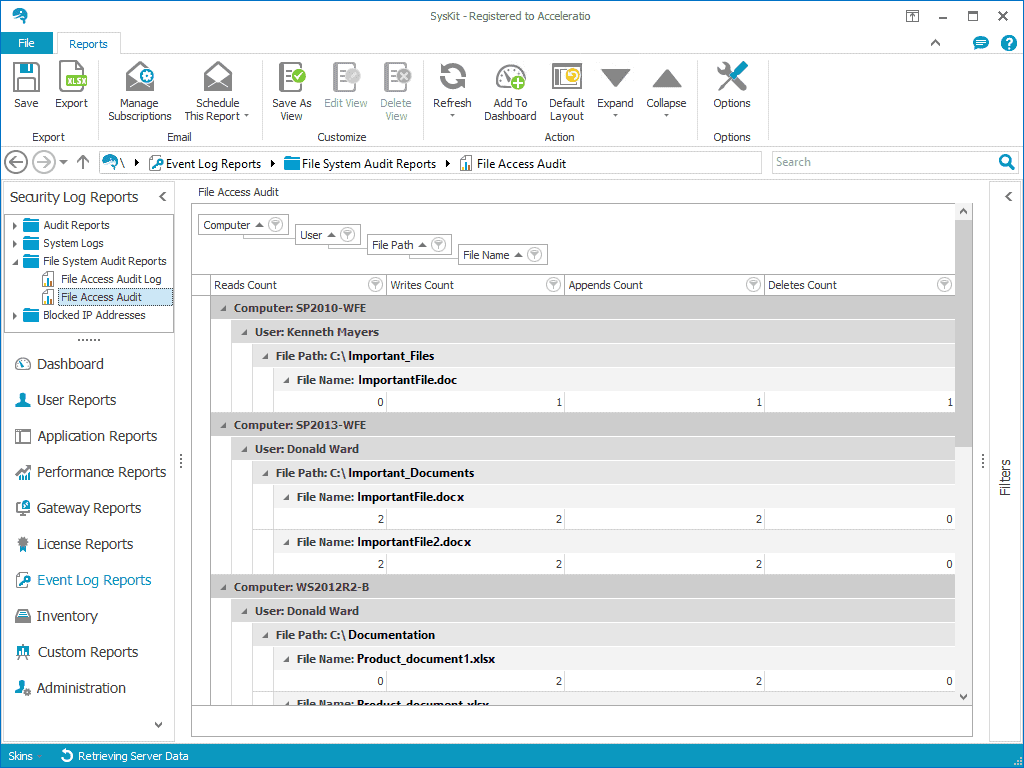
So instead of mulling over the logs you’re trying to keep up with, here’s a solution: Syskit Monitor has Event Log Reports and can help you with Windows file auditing as well!
With this server monitoring and administration tool, you can track all user activities on the file system.
Syskit Monitor gathers information and logs from the Event Log on your servers depending on what kind of auditing policy you have.
Among the File System Audit section, you can find the following reports:
File Access Audit Log – Shows file access history and actions performed on files, as well as the exact time when each action happened.
File Access Audit – Provides a summary of the number of Read, Write, and Update actions per file and user.
Download Syskit Monitor for a free 30-day trial and finally succeed in keeping track of what’s going on in your file system.

