Self-service provisioning in Microsoft 365 – Yes or no?
Table of contents
First, let’s be clear on what self provisioning means. It means that end-users can create their own workspaces like Microsoft Teams, Microsoft 365 Groups, SharePoint Online sites, Planner, etc., without requiring assistance from IT. In a way, you are democratizing Microsoft 365, making it easily accessible to all users and speeding up adoption. But without any guidance and governance, this can lead to a massive number of workspaces with duplication of information and one big group sprawl syndrome, leading to decreased productivity.
In this blog, we will discuss what you need to know about self provisioning to make an informed decision on what is best for your organization. Some options are available out-of-the-box, while others might mean you need a custom solution in place. We are going to ask questions which will help you figure out what you should pick.
Who can create new workspaces in Microsoft 365?
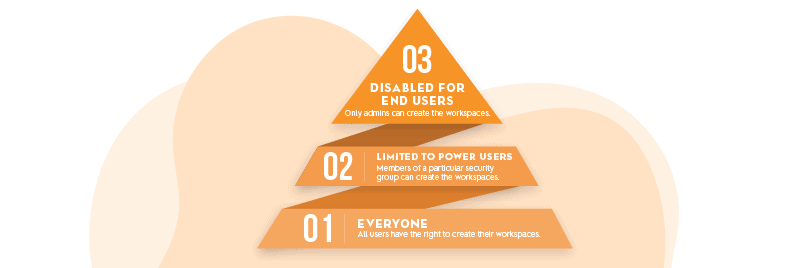
Out of the box, Microsoft 365 offers three options:
- Option 1: Enable creation for all users – this is the default, fully democratic option where all users have the right to create their workspaces.
- Option 2: Allow creation only for members of a particular security group – you can limit workspace creation to a set of power users who have more guidance and training on enforcing governance standards you specify. Keep in mind that for this option, both the admin and members of that particular security group will need an Azure AD Premium license.
- Option 3: Disable creation for all users – only administrators will be able to create new workspaces. You have all the control, but it could lead to the growth of shadow IT. If a user cannot create his own plans in Planner, maybe he will just use Trello instead? Keep in mind that you are not just blocking Microsoft 365 Groups and Teams. You are blocking the creation of all workspaces like Planner, Microsoft Stream, Power BI, Yammer, etc. You will also need an Azure AD Premium license to do this.
So now that you know the three main options, it may seem that your decision is simple, but there are other essential factors you need to consider, more on that below.
What about governance?
During workspace creation, for instance, a Microsoft Team, the end-user gets to decide about some essential things like:
- Team name – this will also translate to the site’s name and mailbox. It’s a good idea to block some words (for example, CEO, HR, or Payroll). You can also add prefix or suffix to the name with attributes like “Department” from AAD. This feature is called naming policy, and it does require Azure AD Premium P1 licenses.
- Public/Private – the user gets to decide on the group privacy and who can join the team/group
- Sensitivity label – if you use them, you can enforce some settings like guest access with them
Out of the box, you also have other premium features like the expiration policy, which does require Azure AD Premium licenses.
If this is all the governance you need and you have Azure AD Premium licenses, then my suggestion would be to stick with the out-of-the-box provisioning options, pick which creation option suits your organization best, and define the mentioned policies.
When should you think about using a custom self provisioning solution?
Let’s go over a couple of use cases where the out-of-the-box solution might fall short, and your only option is a custom solution or a 3rd party product.
Use case 1: Can I limit the creation of Yammer communities?
It might be completely ok that your end-users create their own Teams/Groups, but you might want more control over Yammer communities and the content exposed to the entire company. In that case, you might want to build some approval flow for Yammer communities but leave all other workspace types on self provisioning. This is not possible with out-of-the-box capabilities. You can either provide everything or limit everything – there is no middle ground.
Use case 2: Can I limit the creation of public Teams/Groups?
Having public Teams/Groups can be a risk if users don’t understand the concepts of privacy, and that it means anyone in the company can access the content of that team/group. You might be ok with end-users creating private teams/groups without approval but prefer to have an approval flow to create public ones. This is not possible with the out-of-the-box setup. In general, you cannot enforce different team/group settings during creation as it is up to the user creating it to make those choices with the out-of-the-box self provisioning.
Use case 3: Can I control which sites are used for external collaboration
It is a good idea to have dedicated sites for collaboration with external partners to limit the risk of oversharing. You would want to have a prebuilt template to provision such a site with all the necessary settings or even custom designs, prebuilt pages, libraries, etc. Optionally, you’d like to put an approval process for such sites. Once again, this is not something you can control with out-of-the-box features.
Use case 4: People from the Legal department can only request private sites with the appropriate sensitivity label
All documents and sites produced by the legal department are confidential, so you need to ensure their security. To prevent accidental sharing of these sites, they should be private and have the proper classification. Unfortunately, you cannot use Azure Active Directory attributes like Department to enforce different settings and site templates.
To keep this short, here are some of the most common customizations:
- Predefined sites administrators. You might want to add some IT admins or service accounts as site admins.
- Prebuilt templates for different departments. You might need to apply different templates for different departments, which allow you to customize sites, teams, and groups as they are created. For Teams, you can check out the existing templates. But a lot more is possible. Be sure to check out the PnP provisioning engine.
- Automated governance policies enforcement. The most common policies organizations implement are access reviews, guest user recertification, ownership recertification, or custom expiration criteria. Organizations usually also define the minimum number of owners for each workspace. Having all these processes automated reduces the risk of human errors and increases overall security and productivity.
Final verdict on self provisioning
Now that you have seen the out-of-the-box options and limits, you have all the information to make a decision for your company. There is no single right answer. It all depends on your needs. It will be somewhere in the middle ground for most organizations where end users can do most things without IT’s assistance, with IT keeping things under control, especially for those riskier workspaces ensuring you have the proper governance in place.
If out-of-the-box features meet your requirements, go no further. However, if you have other requirements, you need to consider building a custom solution or investing in a 3rd party tool. Whichever option you choose, think about your users. Make things easy for them and keep them inside Microsoft 365, even when using a custom solution. You can also check out different samples like Microsoft’s Request-a-team app as a good starting point.
If building and maintaining your own solution seems like too big of an effort, look at the Office 365 provisioning options inside Syskit Point. It’s an easy plug-and-play solution with a Teams app, so your users don’t have to leave the familiar workspace to get things done.
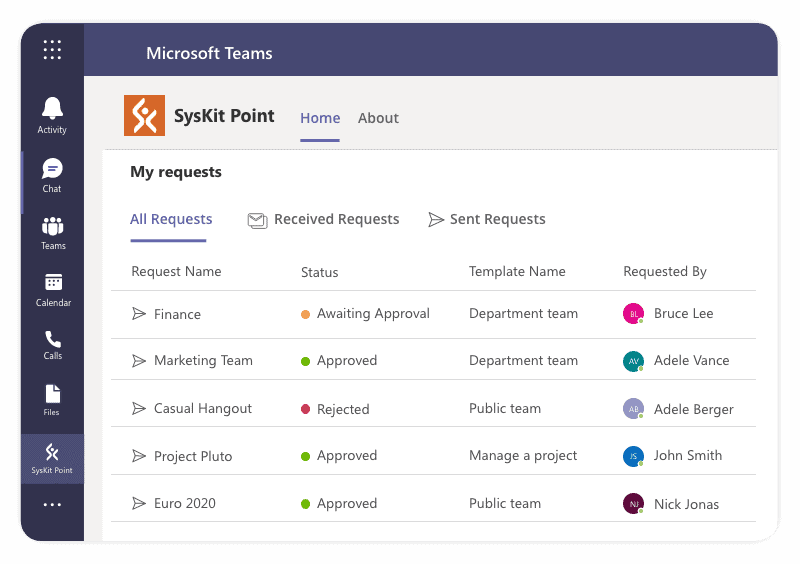
Use customized provisioning templates to take control of your Microsoft 365 workspaces creation. Quickly establish compliance from the beginning of the lifecycle and enforce company security policies. If you want to learn more about how to effectively introduce self provisioning without risking uncontrolled sprawl take a look at our Microsoft 365 sprawl webinar or read our detailed data sprawl eBook.