M365 security risks don’t spike. They accumulate.
Your Microsoft 365 exposure isn’t growing because of attackers. It’s growing because of oversharing, forgotten workspaces, and permissions no one reviewed.
And most teams don’t see it until it’s too late.
Protect sensitive data in Microsoft 365 without overwhelming IT
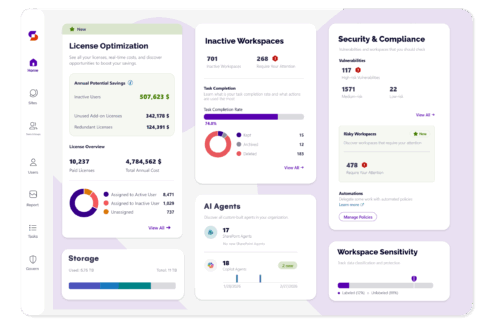
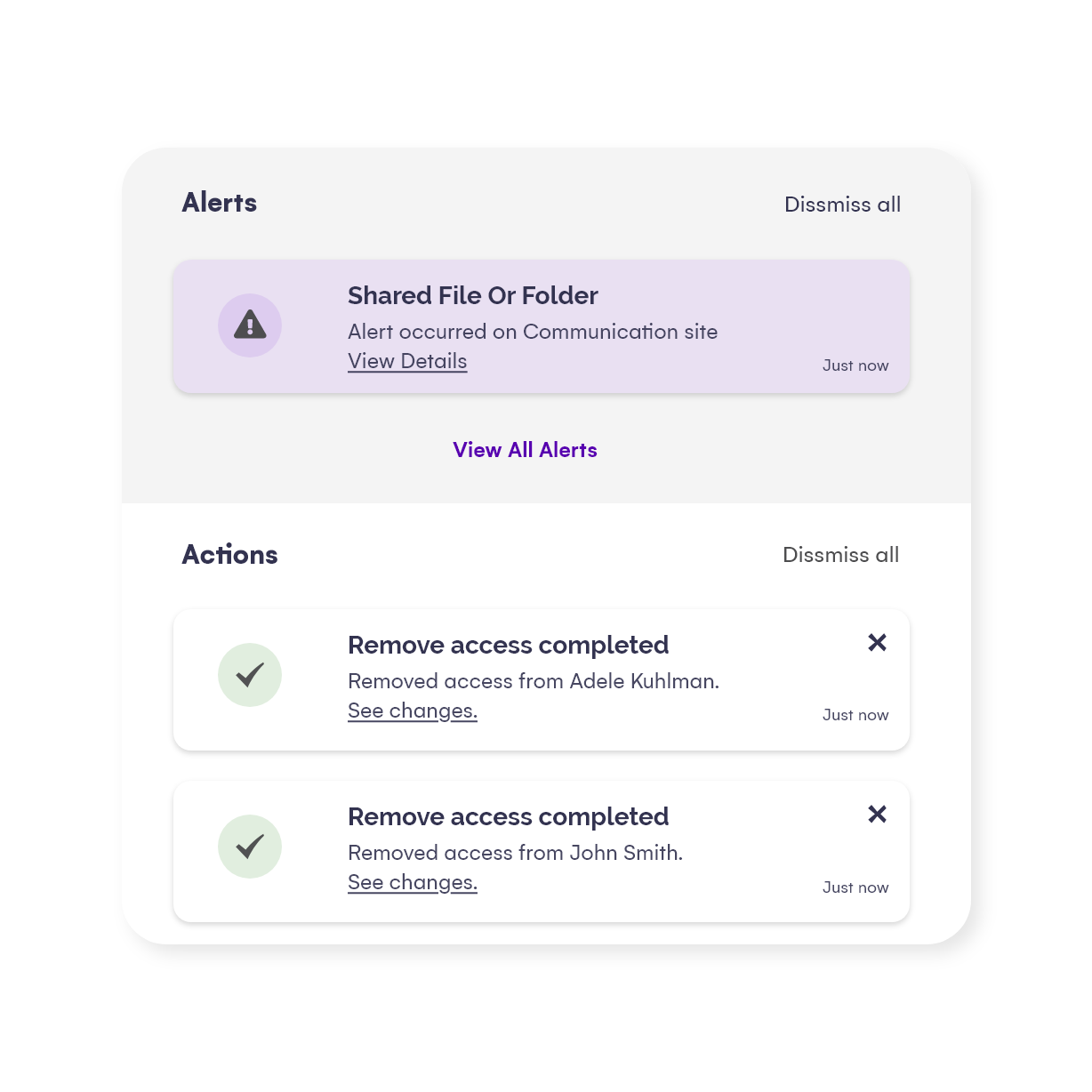
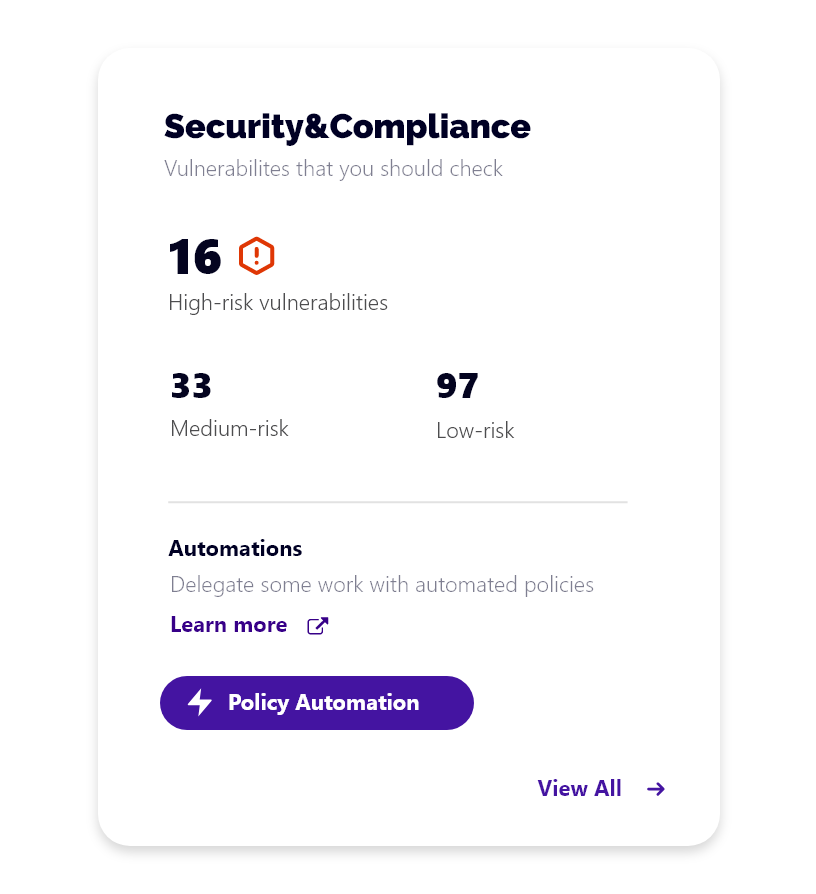
Syskit Point gives you continuous security monitoring and insights that show exactly where exposure is building. Before it becomes an incident. It gives you visibility into sensitive access across Microsoft 365 — including Teams, SharePoint, OneDrive, and the Power Platform — helping assign ownership and catch risks early.
With dashboards, access reviews, and oversharing alerts, you can monitor data exposure at scale and report clearly to business leaders.
See which workspaces are your biggest liability
- Flag workspaces with sensitive files shared with anyone or company-wide and understand why.
- Surface content exposed to broad groups (Everyone / Everyone except external users).
- Identify ownership gaps — too many owners, too few, or none at all.
- Remediate directly: change owners, archive workspaces, remove risky links.
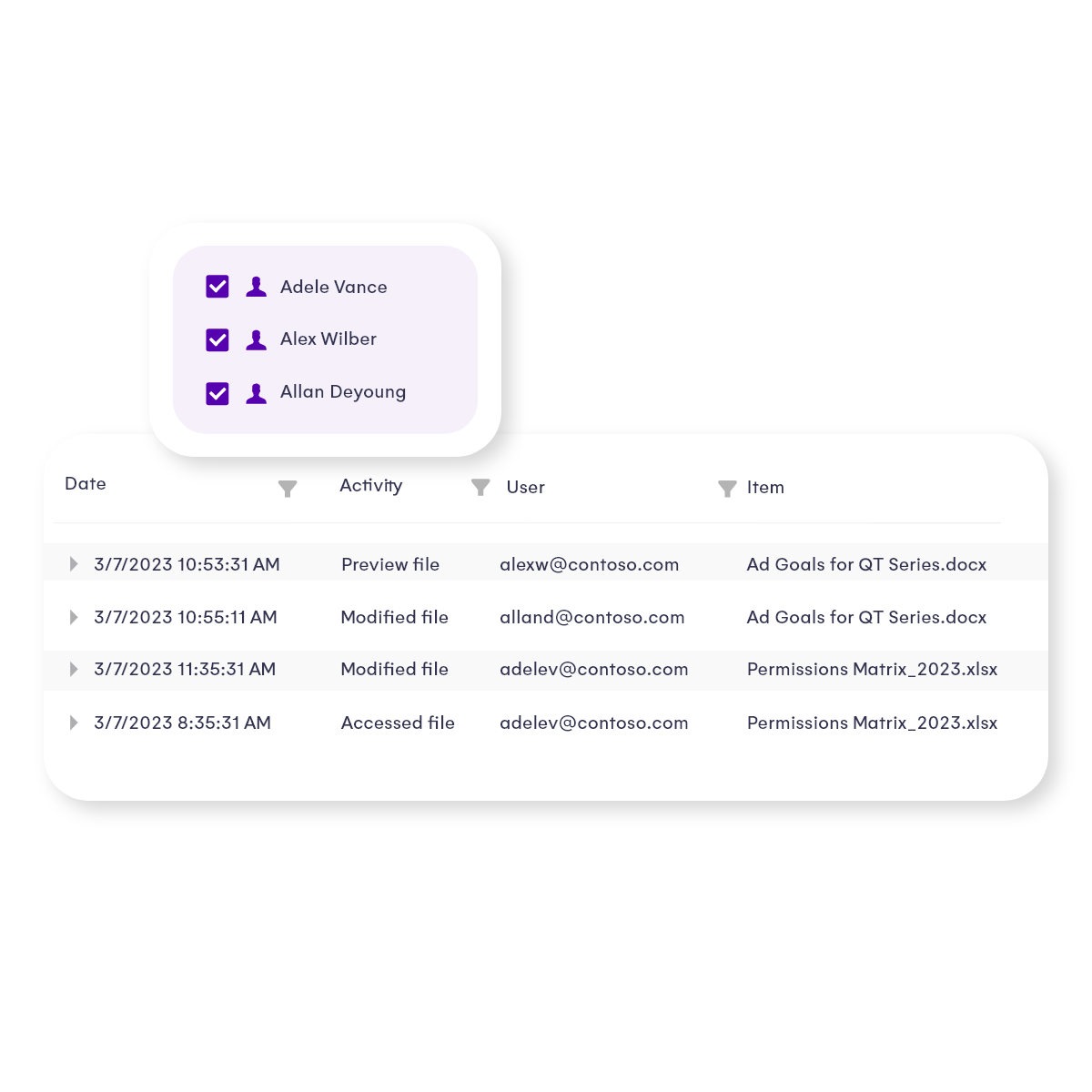
Audit SharePoint permissions and monitor sensitive access
- Track who has access to sensitive content across Microsoft 365 — including SharePoint, Teams, OneDrive, and Power Platform.
- Identify over-permissioned users, dormant owners, and external guests with lingering access.
- Highlight sites and documents with excessive exposure before they become a breach risk.
- Maintain visibility and control without needing to dig through PowerShell logs or admin portals.
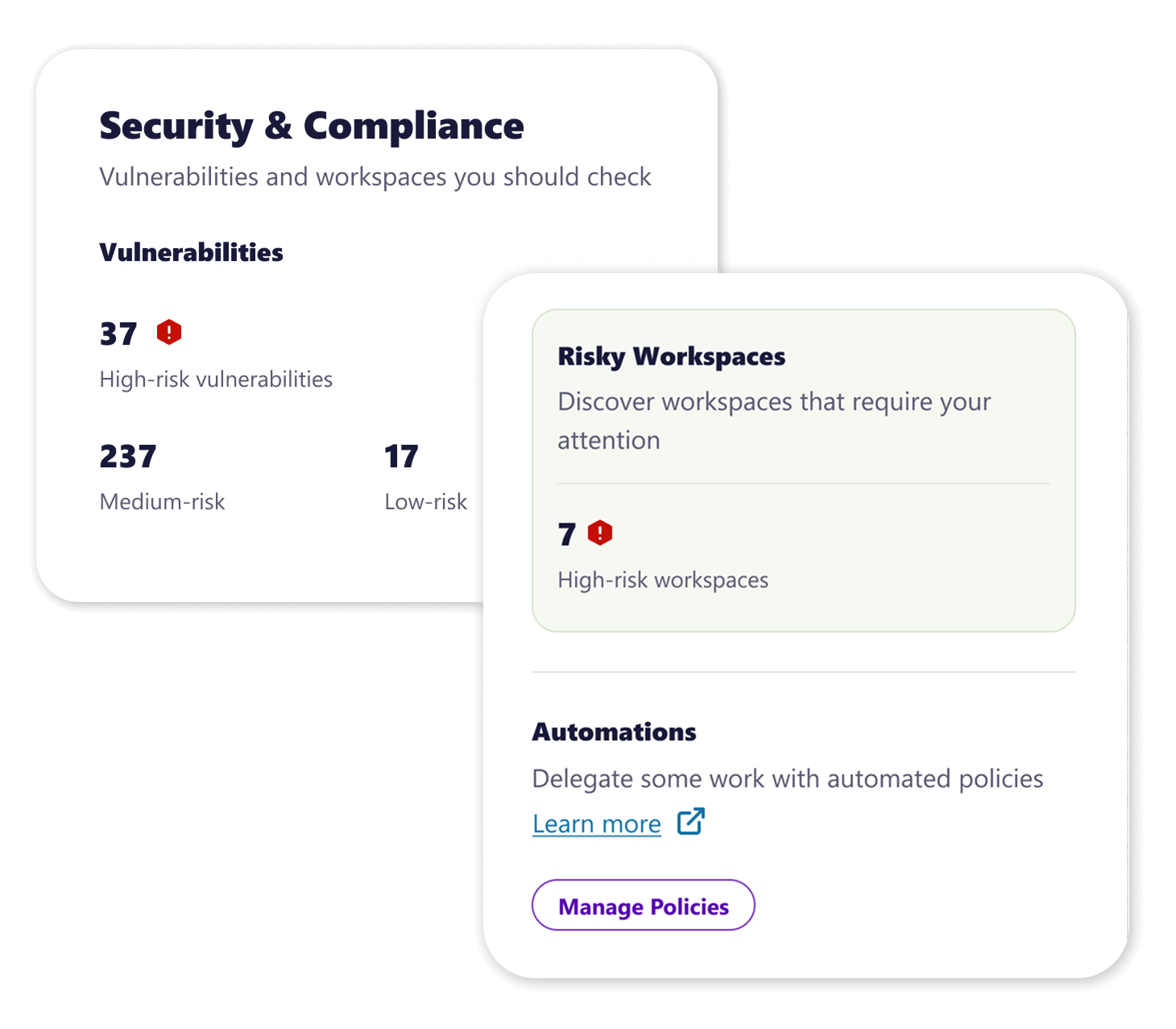
Detect risky activity and catch external sharing before it escalates
- Get alerted to suspicious access patterns, oversharing, and unreviewed guest access.
- Detect anomalies like privilege creep or unchecked Team and Group sprawl.
- Spot when security policies are being bypassed or ignored in high-risk areas.
- Empower security teams to act before risk turns into impact — without disrupting end users.
Report Microsoft 365 security risk clearly to leadership
- Generate real-time dashboards that show where data is exposed and who owns the risk.
- Provide executives and security leaders with clear, metrics-based insights into access posture.
- Demonstrate how governance actions are reducing data risk over time.
- Justify security investments by making risk visible and accountability traceable.
Trusted by